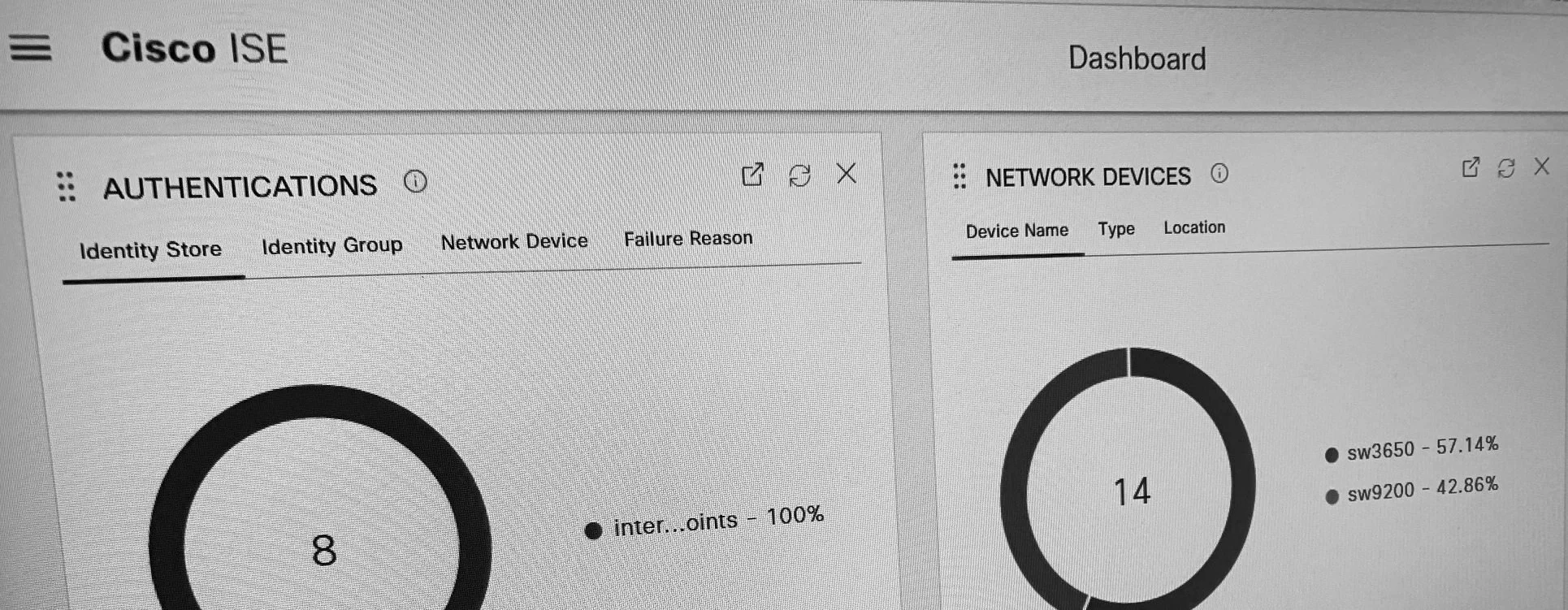
In this short article, we take a look at how to create a Redirection ACL on 9800 WLCs to use with Central Web Authentication for Cisco ISE guest access services and go through what each line of the ACL really does.
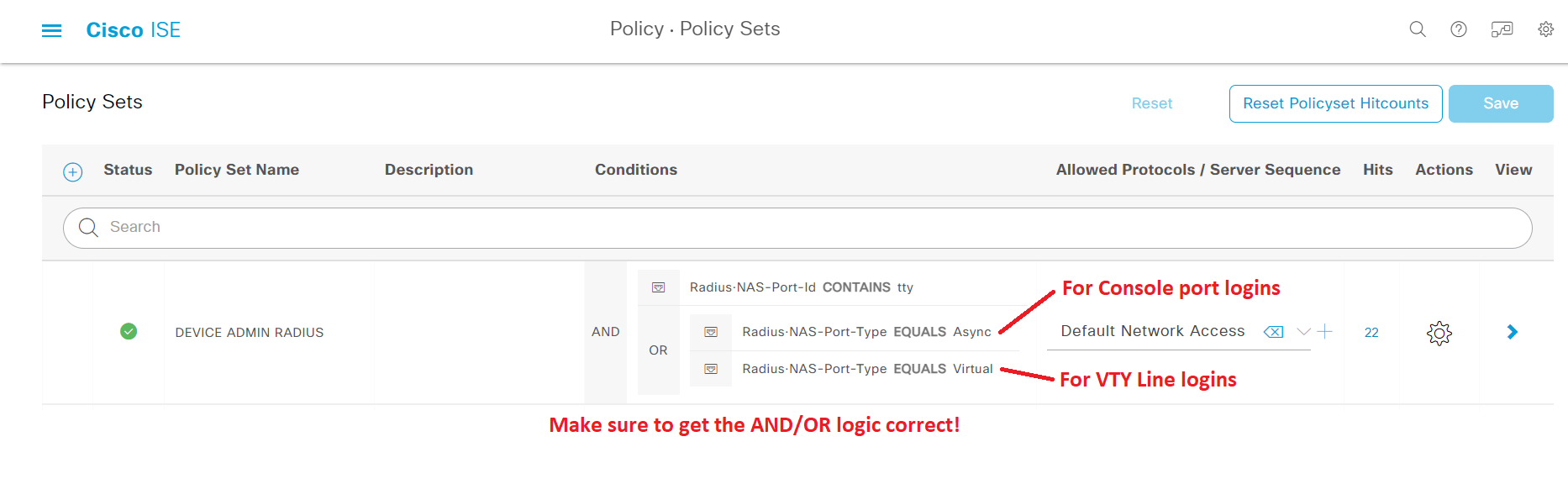
In this article, we look at how to configure Cisco ISE as a RADIUS server to handle authentication requests for controlling access to network devices, both for network administrators with full access and for helpdesk personnel with limited access.
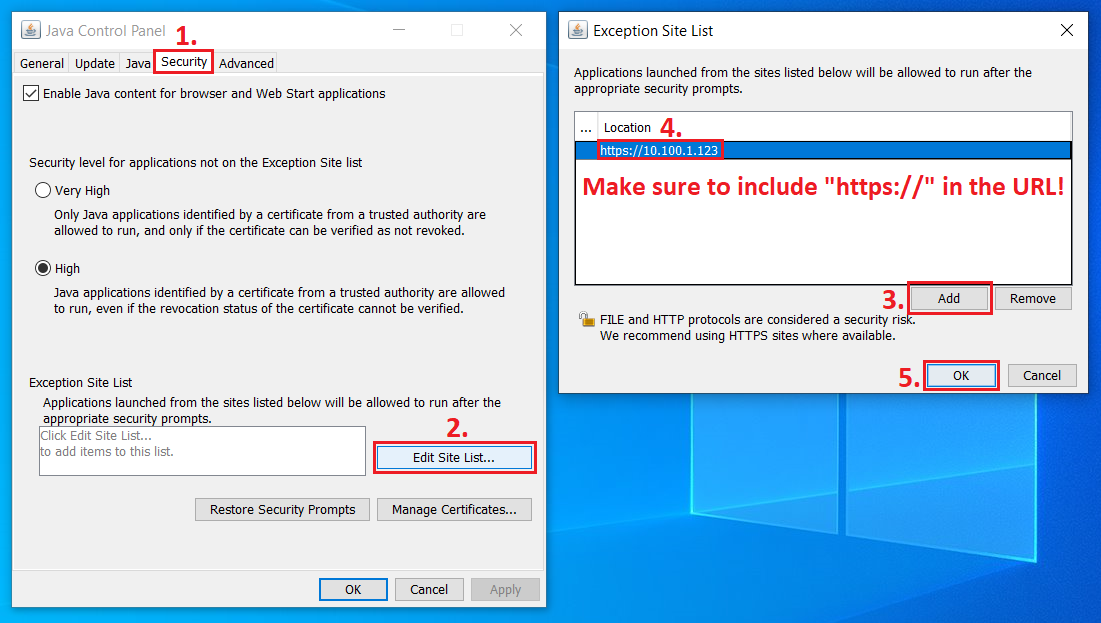
In this article, we take a look at how to configure Java to get Java-based KVM up and running to remotely perform a re-imaging of the Cisco ISE application on physical SNS servers.
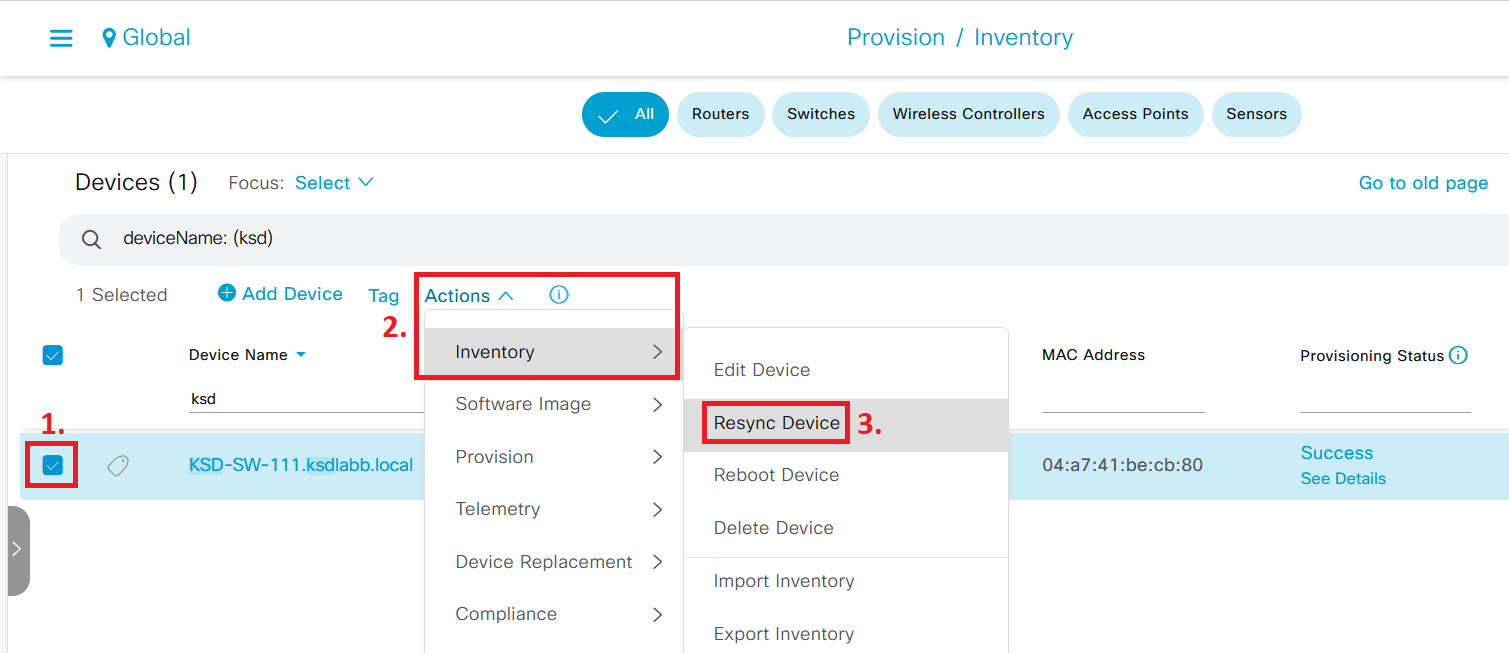
With the rise of powerful network monitoring and automation systems, like Cisco DNA Center, network devices are constantly crawled for status updates. In this article, we look at how this could affect TACACS+ services running on Cisco ISE and what you can do to optimize your deployment.
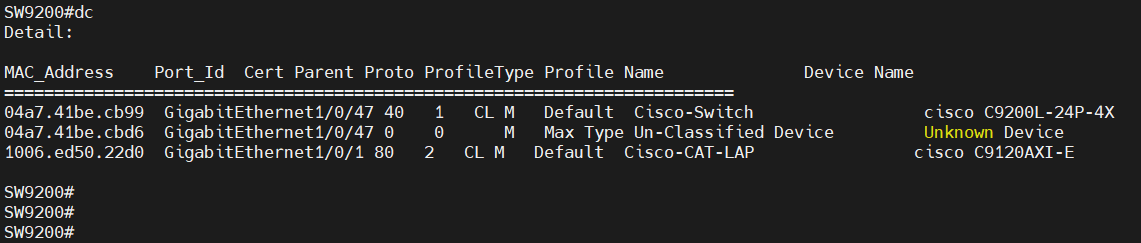
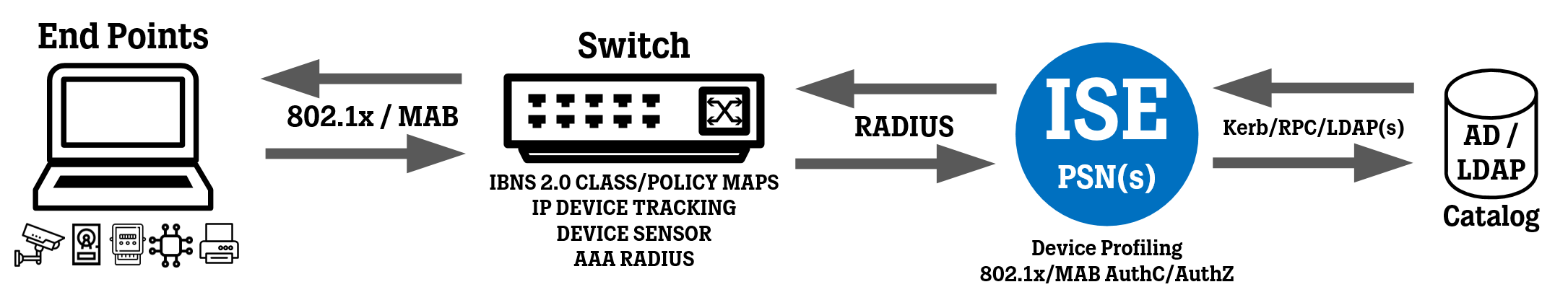
In this article, we take a look at some of the most important “show” commands used when implementing IBNS 2.0 for 802.1x and MAB authentication on Cisco switches, and how to configure Aliases for these commands to dramatically improve time spent on troubleshooting and verification.
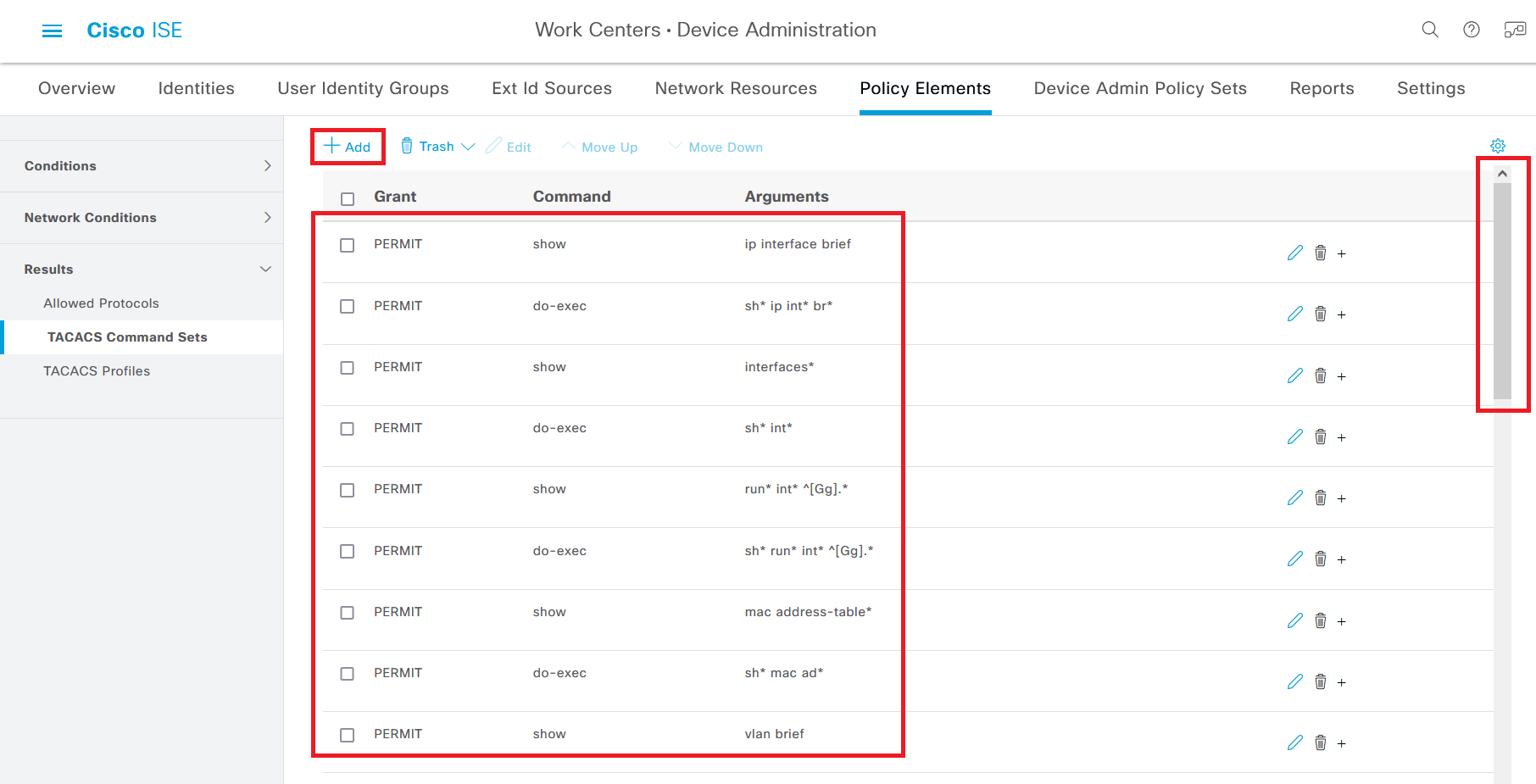
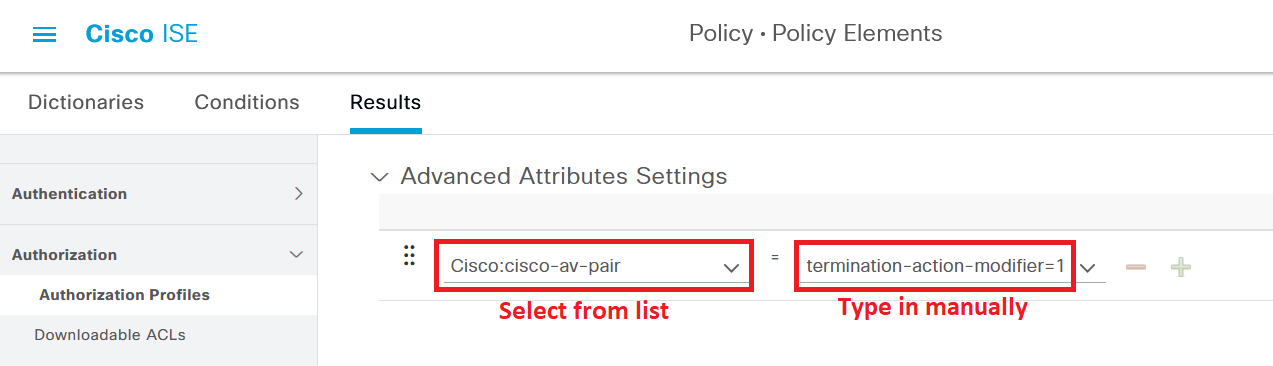
In this article, we take a look at how to configure a TACACS Command Set in Cisco ISE to enable non-administrator staff to use both show commands and configuration commands related to certain interfaces (typically access ports).
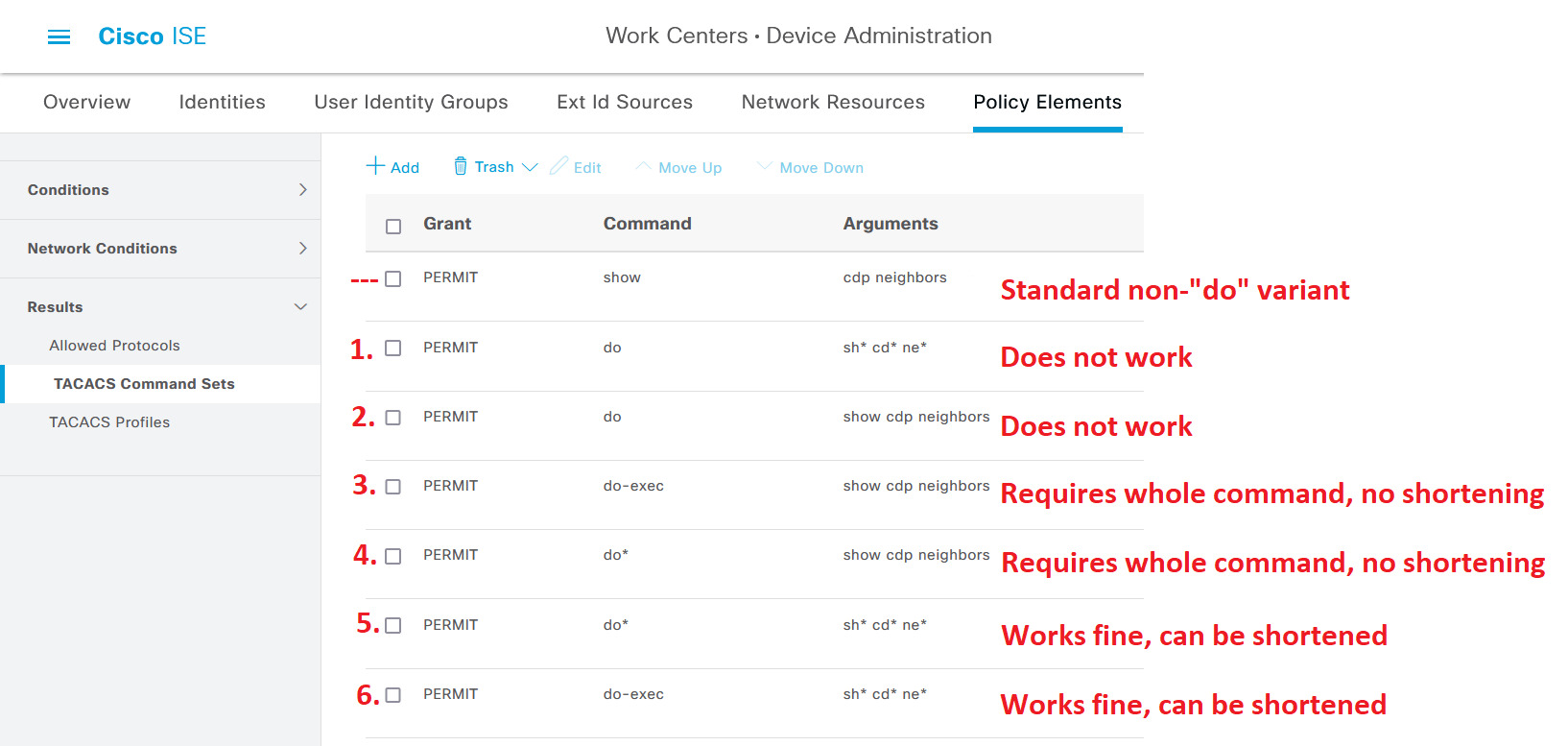
In this article, we are going to take a look at different approaches to enable network administrators to use the “do” command on Cisco network devices where TACACS+ authentication is configured using Cisco ISE.
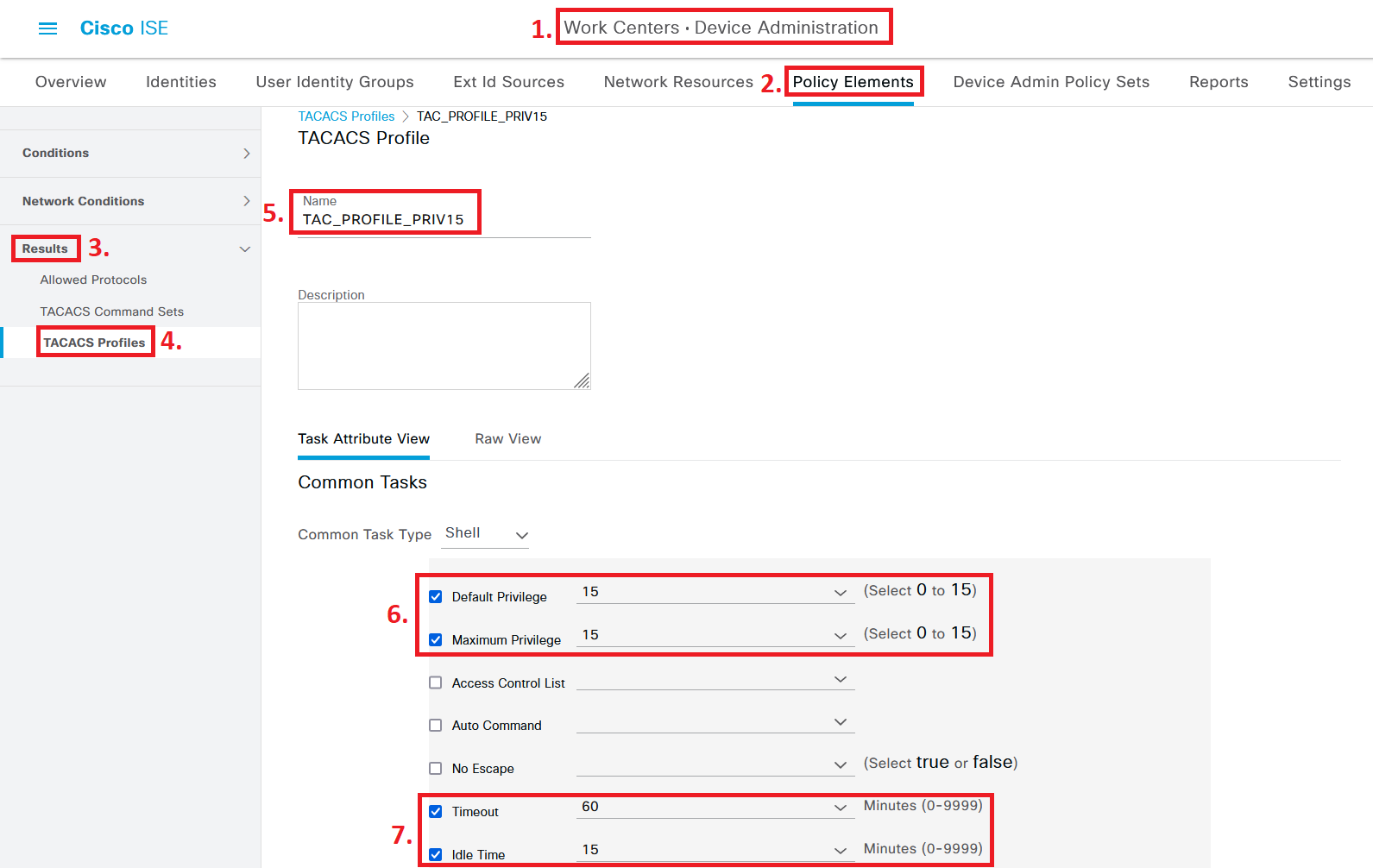
In this article, we take a look at how to configure Cisco ISE as a TACACS+ server to handle authentication requests for controlling access to network devices, both for network administrators with full access and for helpdesk personnel with limited access.
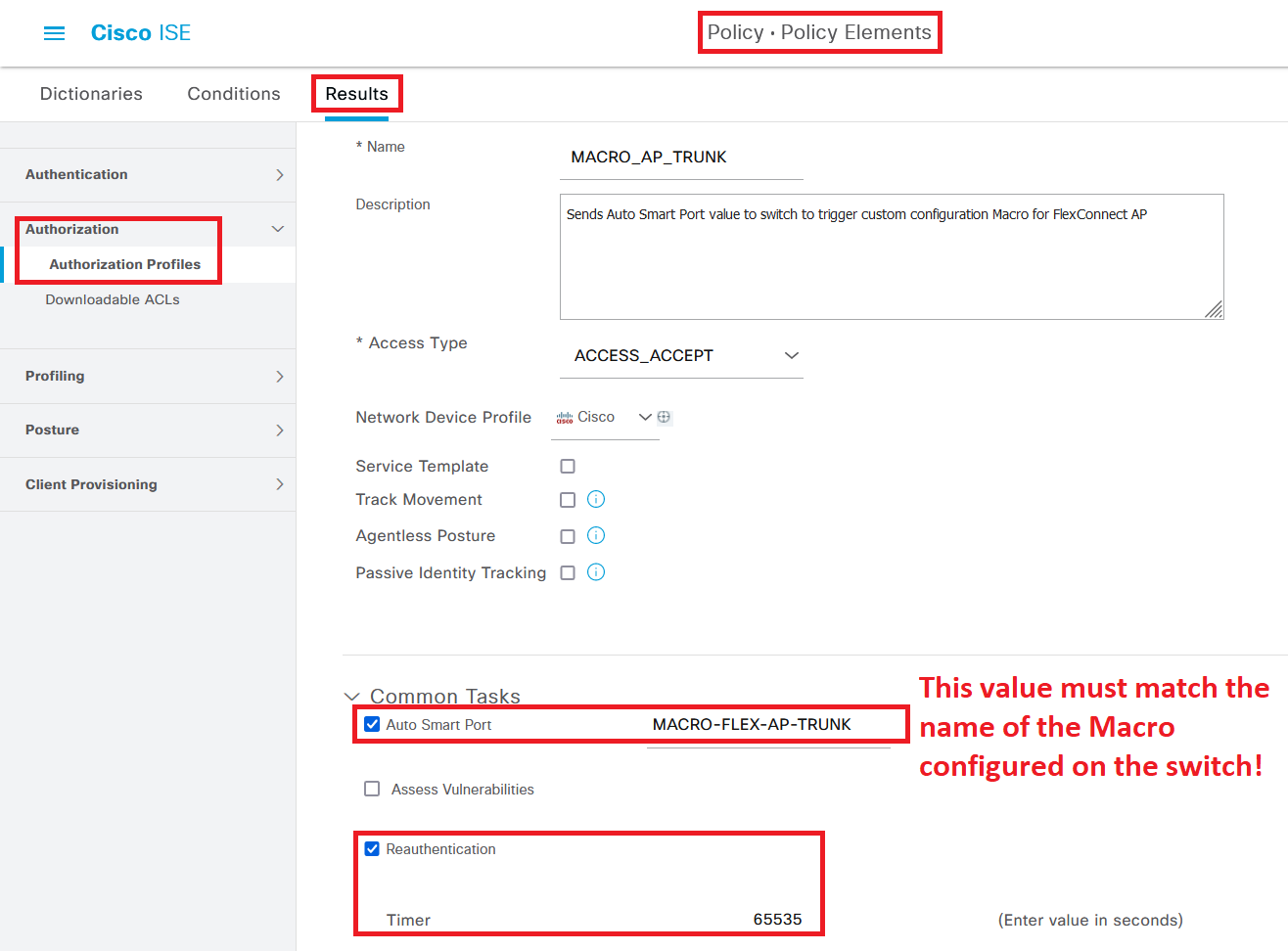
In this article, we take a look at how to make ISE configure a switch port as a Trunk (using a Macro) when an Access Point in FlexConnect mode is connected to an 802.1x/MAB-enabled switch access port, and reverting the configuration back to an access port if the Access Point is unplugged.
In this article, we take a look at a couple of commands that can help your Cisco IBNS 2.0 implementation by going into detail about which kind of events are matched in your Policy Map as endpoints are connected to the network and go through the authentication process.
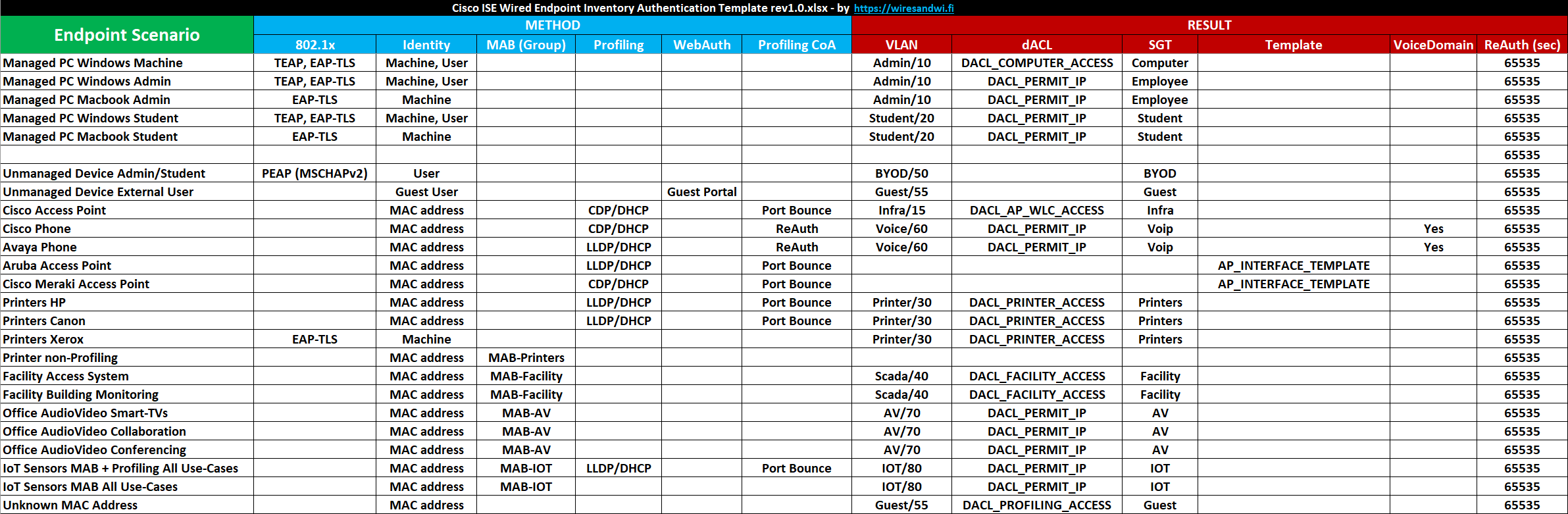
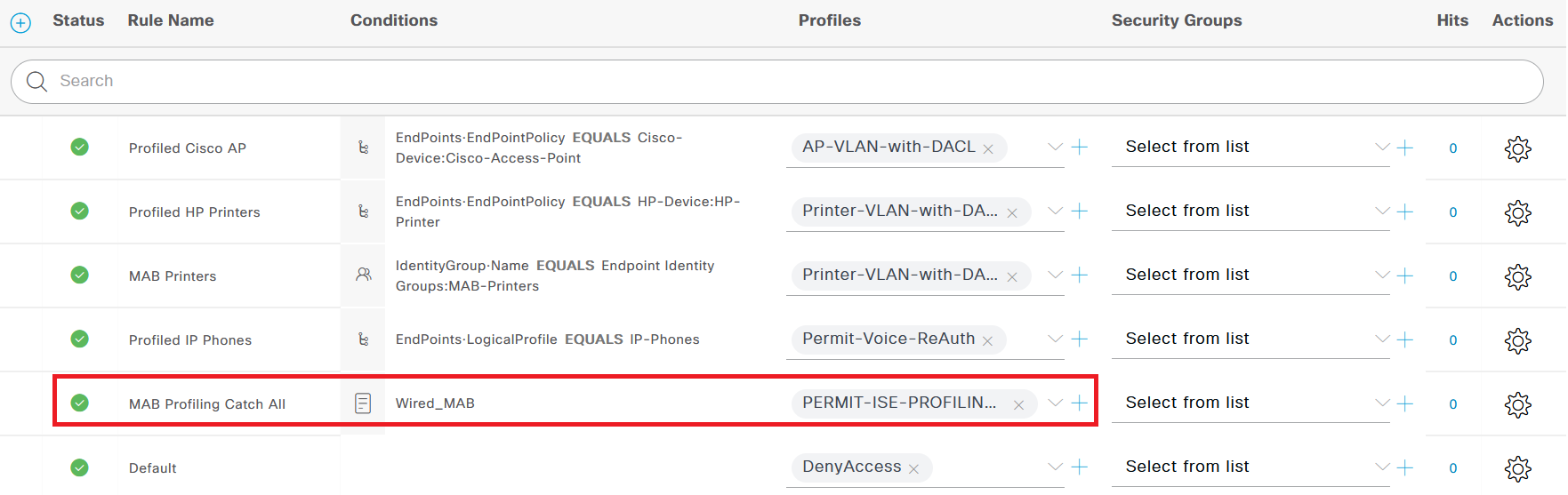
In this article, I share a template you can use for your wired ISE deployments to document which types of endpoints you have in your network, how they will authenticate to the network, and which type of network access they will be granted post-authentication.
In this article, we take a look at a configuration template for deploying IBNS 2.0 Concurrent 802.1x and MAB authentication on Cisco IOS-XE switches, complete with global configuration such as Class Maps, Policy Maps, and Interface configuration.
In this article, we take a look at a configuration template for deploying IBNS 2.0 Concurrent 802.1x and MAB authentication on Cisco IOS switches, complete with global configuration such as Class Maps, Policy Maps, and Interface configuration.
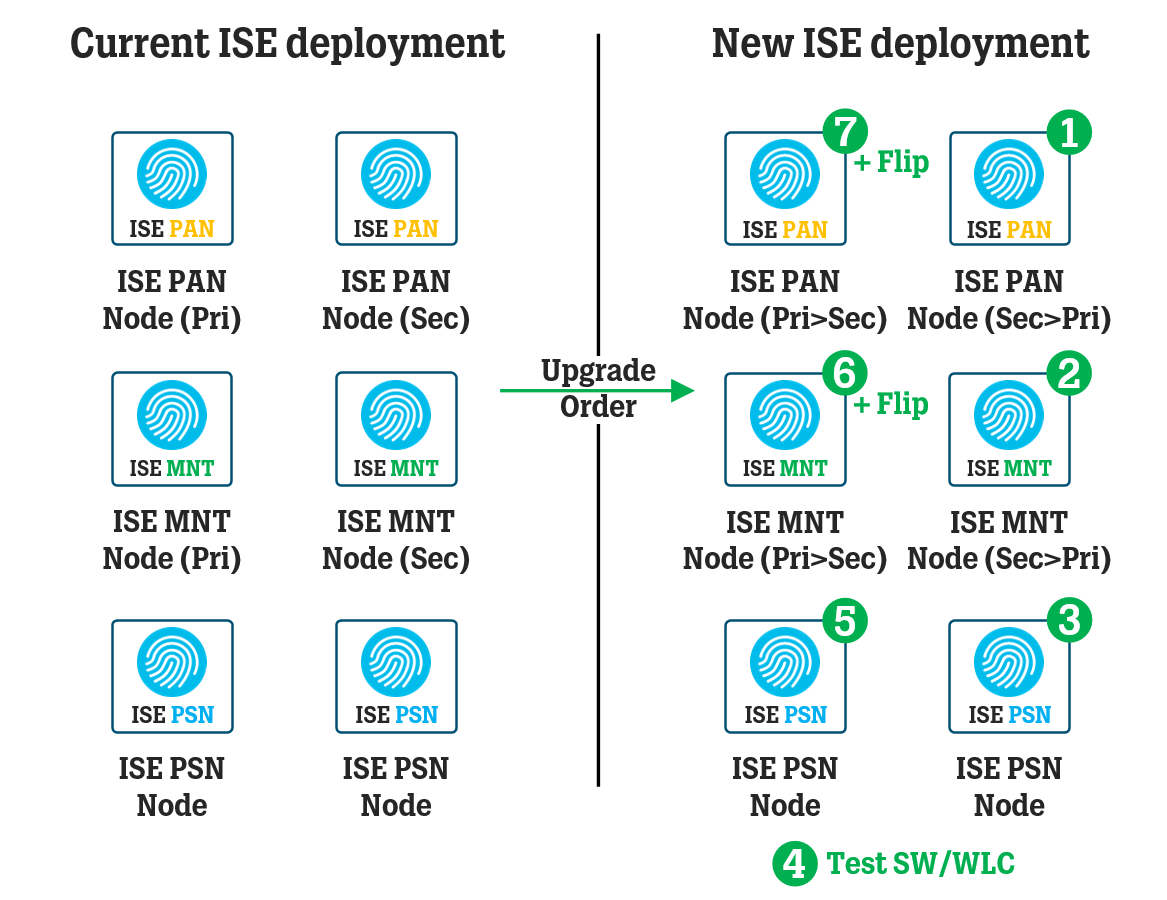
In this article, we take a look at the general steps and processes for upgrading an ISE deployment using the Backup and Restore method, where each ISE node is re-imaged to the new version instead of upgrading existing nodes.
In this article, we take a look at how you can use an Access Control List (“ACL”) to control your ISE PSN nodes available for RADIUS/TACACS communication and how to set up a testing environment halfway through the ISE deployment upgrade process.
In this article, we take a look at a quick fix for the Queue Link Error alarm message resulting in empty RADIUS and TACACS Live Logs and an empty System Summary widget on the front page Dashboard inside Cisco ISE.
In this article, we take a look at what turned out to be a tricky re-imaging process of Cisco ISE 3.1 on SNS servers and how to work around the installation process getting stuck at various stages.
This article goes through some good-to-know general settings and logic to implement for most 802.1x/MAB deployments on wired infrastructure using Cisco ISE. This article focuses on the different Modes (Monitor/Closed/Low-Impact) you can deploy your switches in.
This article goes through some good-to-know general settings and logic to implement for most 802.1x/MAB deployments on wired infrastructure using Cisco ISE. This article focuses on general things to consider when going through your wired deployment.
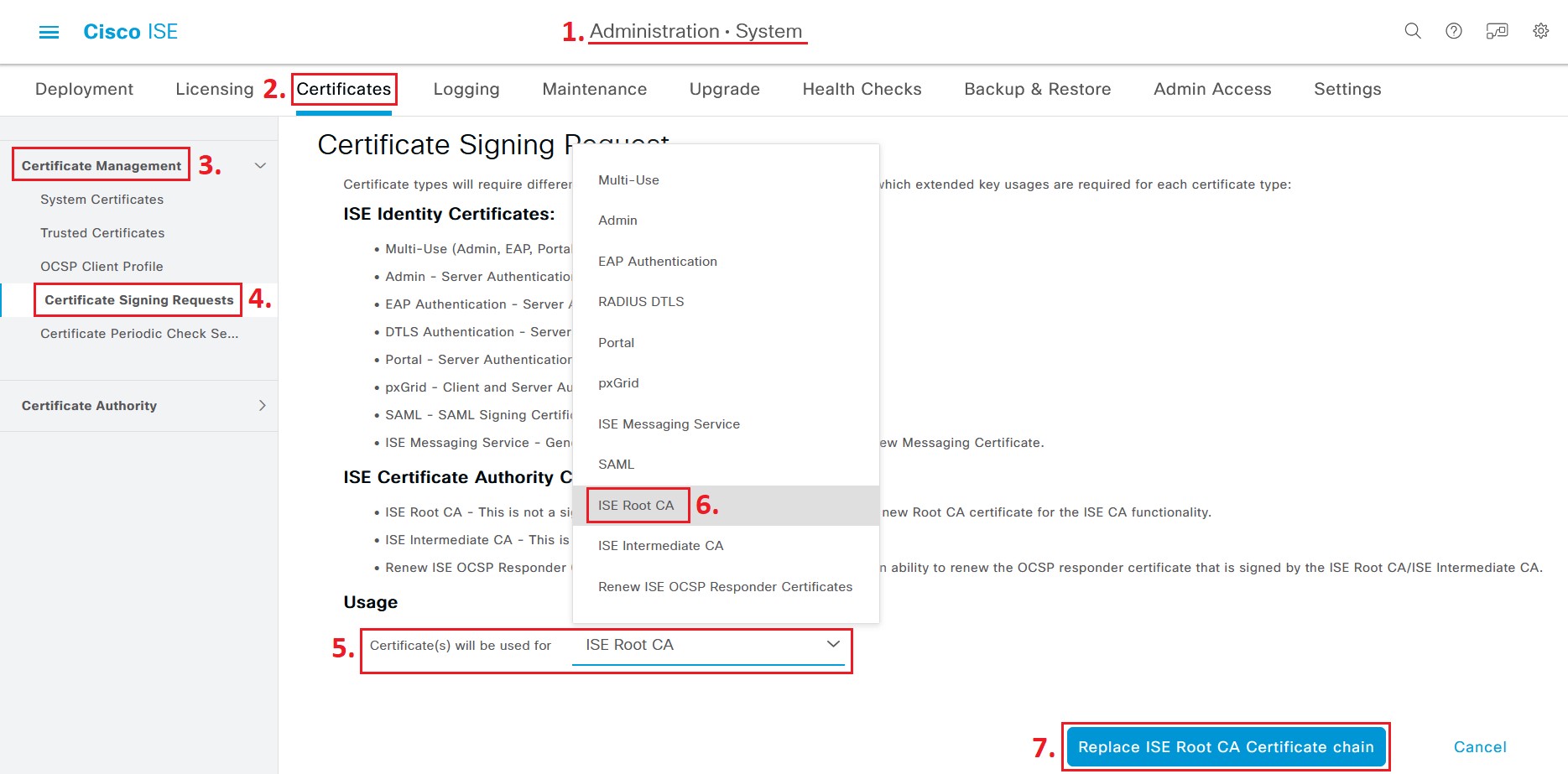
In this article, we take a look at certificate requirements in Cisco ISE, specifically related to the different Extended Key Usages (“EKU”) available which you may need to communicate to your certificate management people before an ISE certificate is issued.
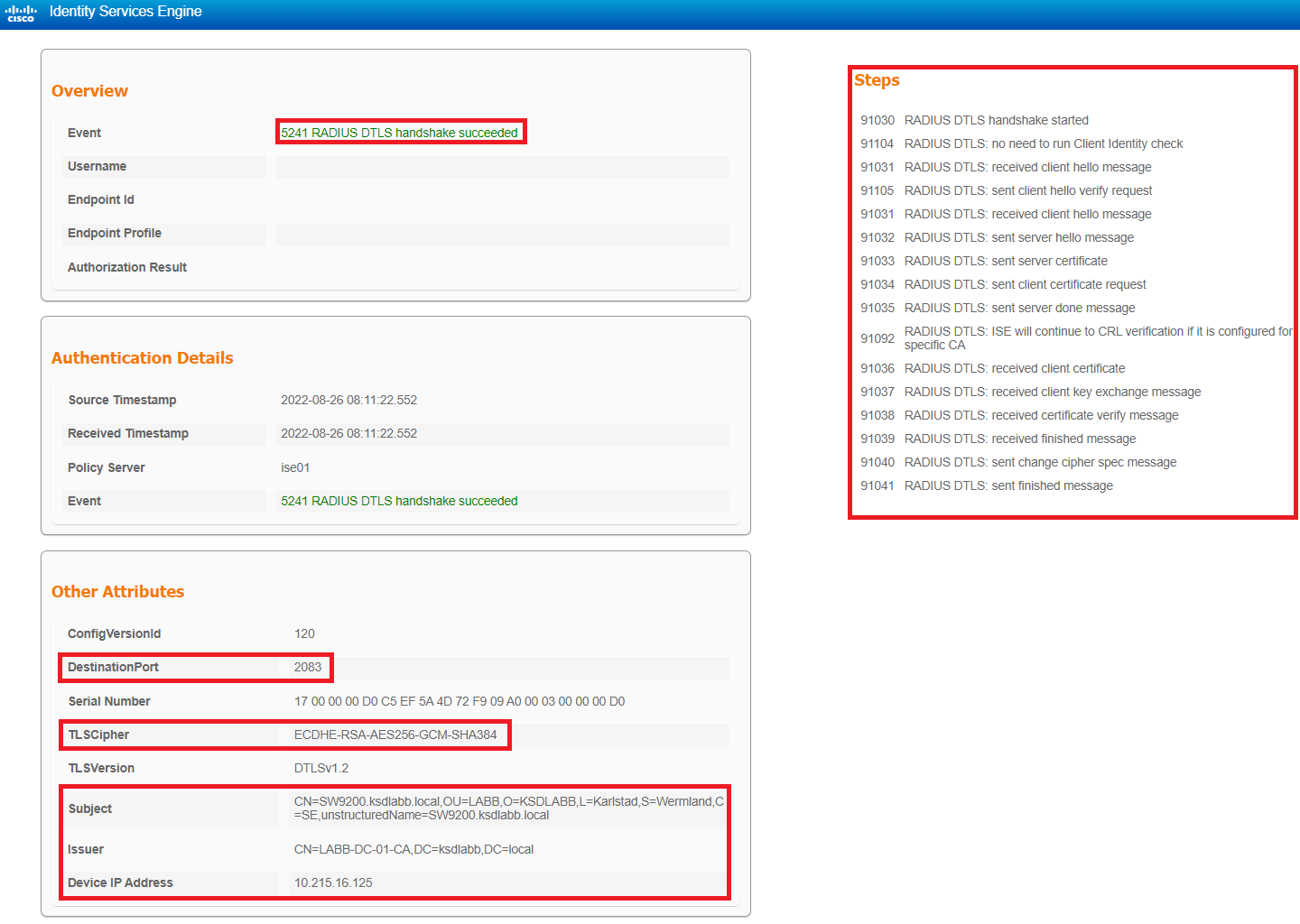
In this article, we will go through various ways to test and troubleshoot the RadSec configuration configured in the previous articles and go through some of the most useful show commands to verify your configuration.
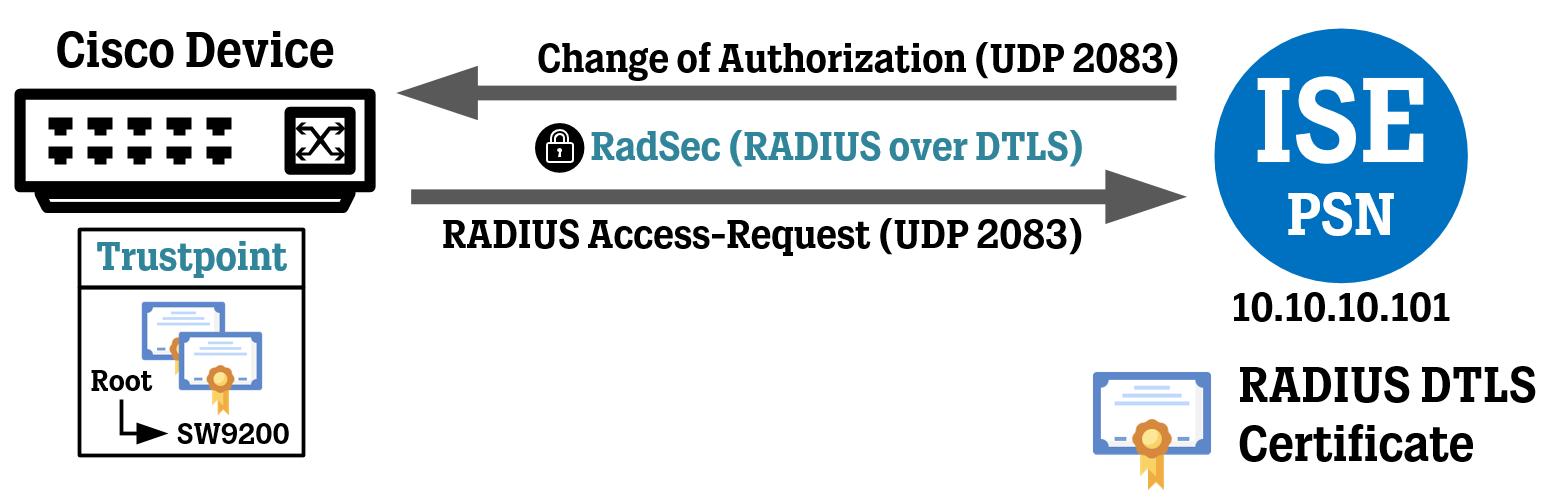
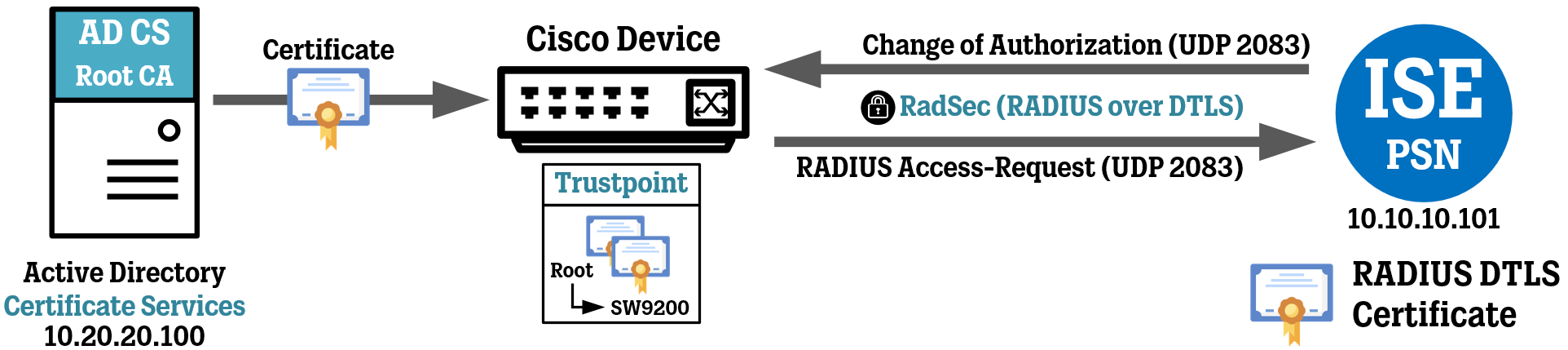
In this article, we will configure a Cisco device (a switch) to communicate using RadSec (RADIUS over DTLS) to Cisco ISE using certificates for mutual authentication between the two sides.
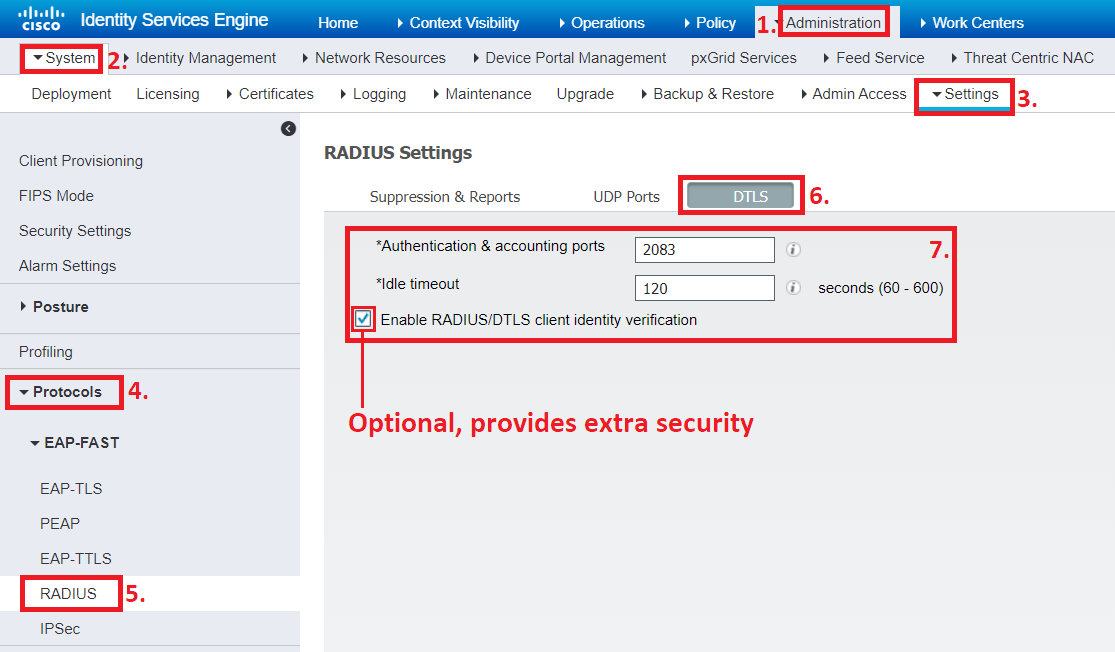
In this article, we will go through the configuration of Cisco ISE to communicate using RadSec (RADIUS over DTLS) to our Cisco device. This cover both general settings and settings related to specific Network Devices.
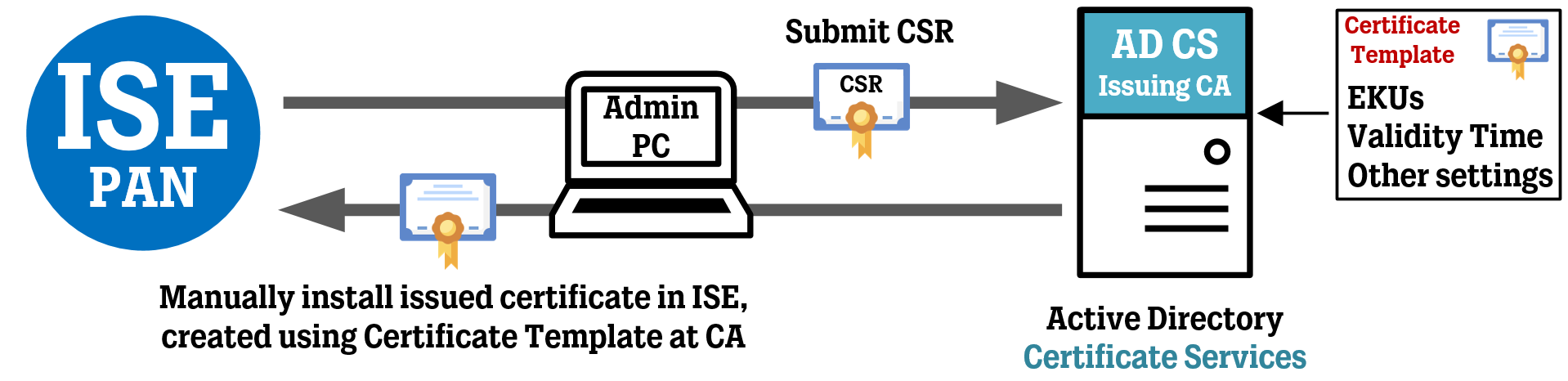
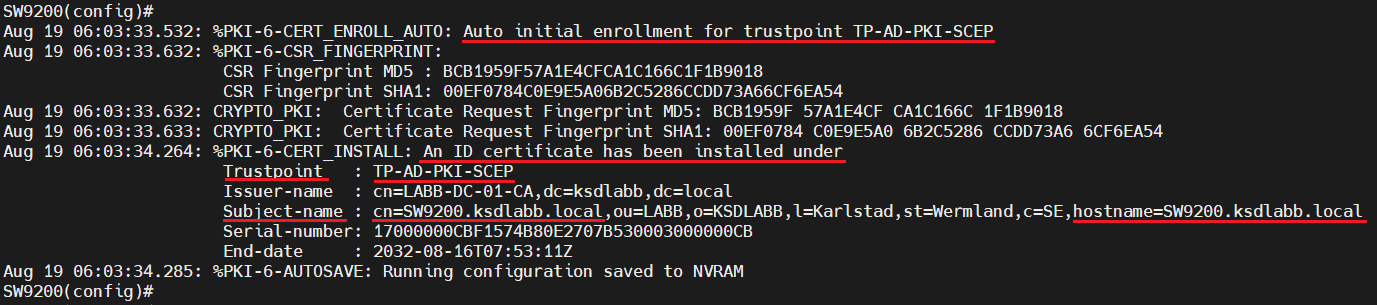
In this article, we will be using the Simple Certificate Enrollment Protocol ("SCEP") feature of the Network Device Enrollment Services ("NDES") within the Active Directory Certificate Services to automatically enroll a Cisco switch to get a certificate issued to it for use with RadSec.
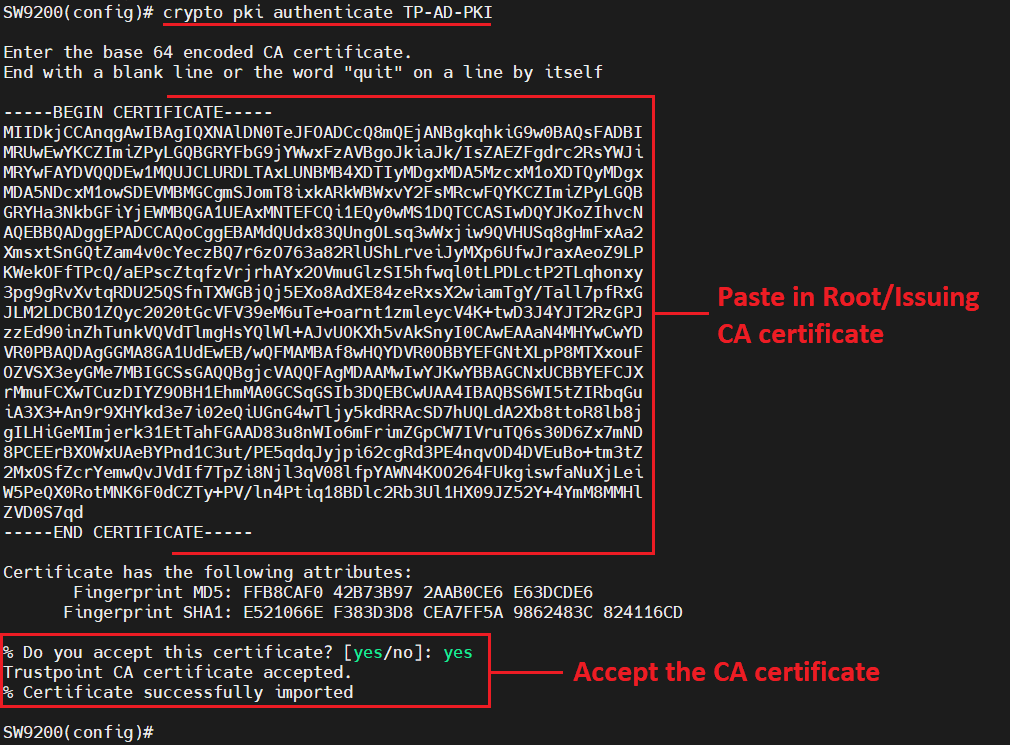
In this article, we will be going through the process of using the Web Enrollment feature of Certificate Services to manually enroll a Cisco switch to get a certificate issued to it for use with RadSec.
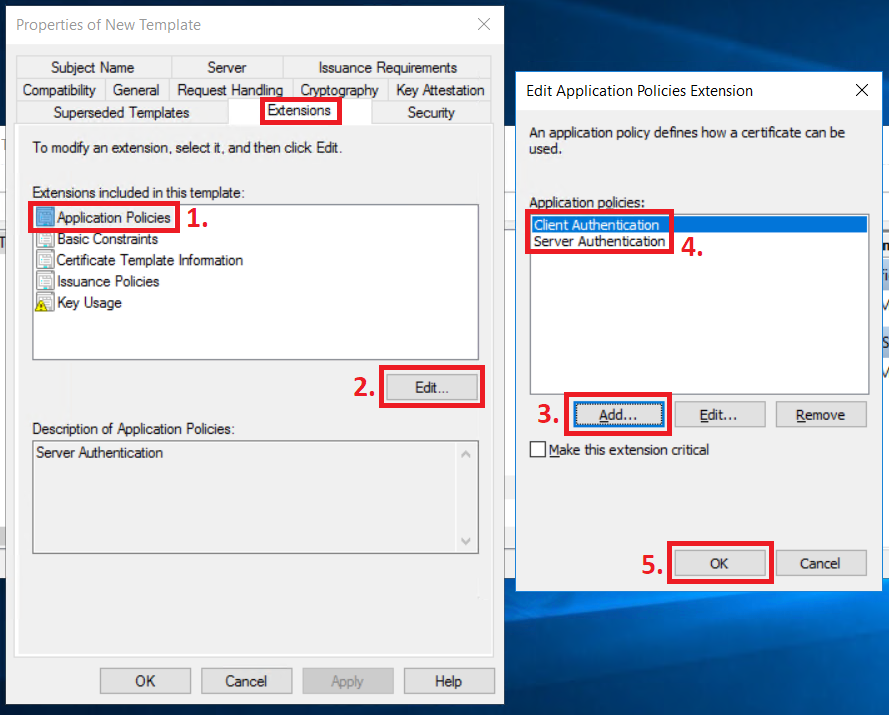
In this article, we take a look at how you can create a Certificate Template for use with RadSec and enroll your Network Devices using the Web Enrollment service of Microsoft’s Active Directory Certificate Services.
This article is the startup point of a complete RadSec (RADIUS over TLS/DTLS) configuration using a Cisco device (switch), Cisco ISE and using Microsoft’s Active Directory Certificate Services to issue the certificates needed, both using the manual approach and automated approach with the SCEP protocol.
In this article, we take a look at a configuration template for deploying IBNS 2.0 802.1x and MAB authentication on Cisco IOS-XE switches, complete with global configuration such as Class Maps, Policy Maps, and Interface configuration.
In this article, we take a look at a configuration template for deploying IBNS 2.0 802.1x and MAB authentication on Cisco IOS switches, complete with global configuration such as Class Maps, Policy Maps, and Interface configuration.
In this article, we take a look at a configuration template for deploying AAA TACACS+ for administrator access and general password and remote access settings on Cisco switches and routers.
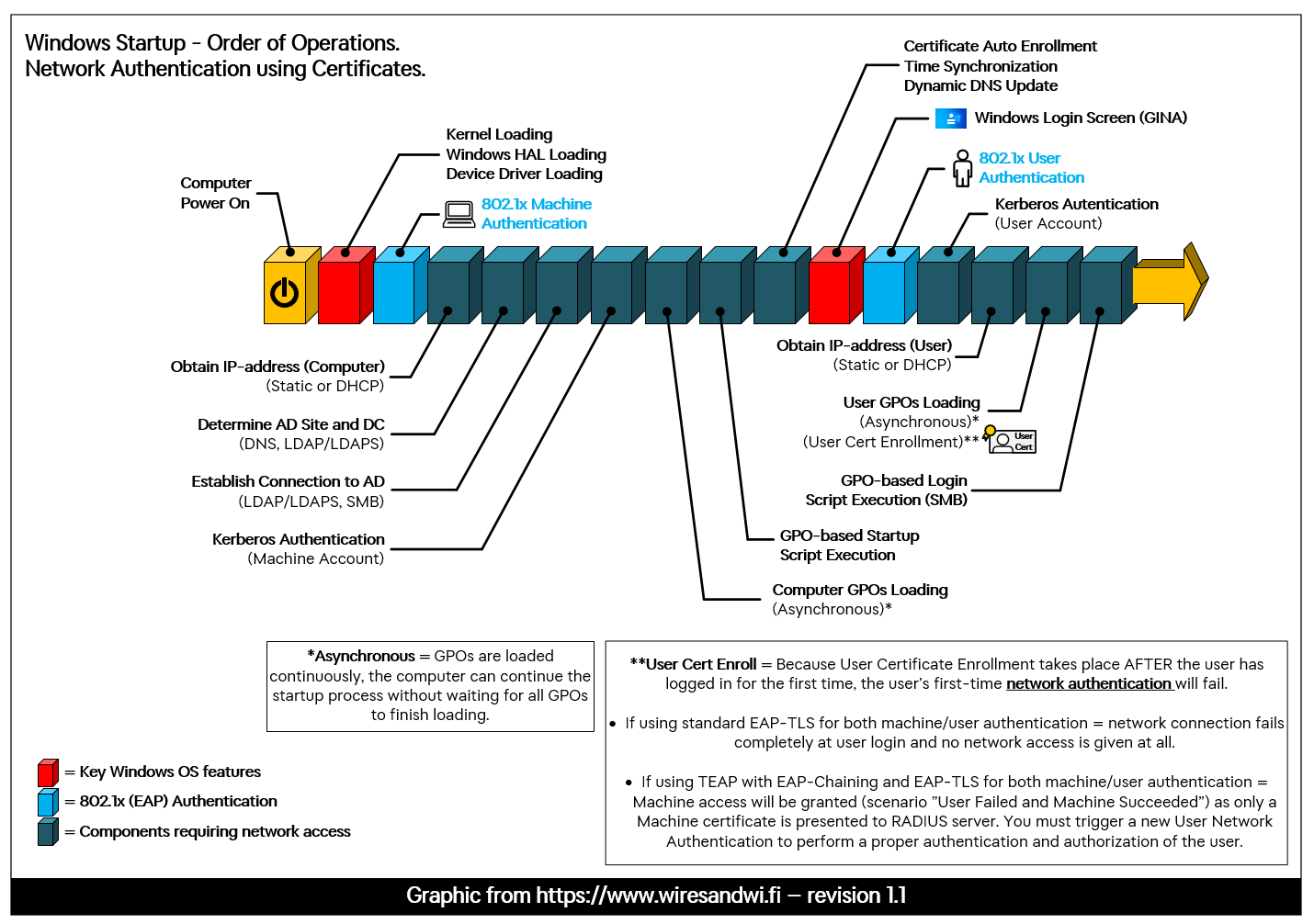
In this article, we take a look at the Windows startup sequence, how it affects both machine and user network authentication, and why it has one major weakness. We also take a quick look at why deploying TEAP instead of standard EAP-TLS might be a step in the right direction.
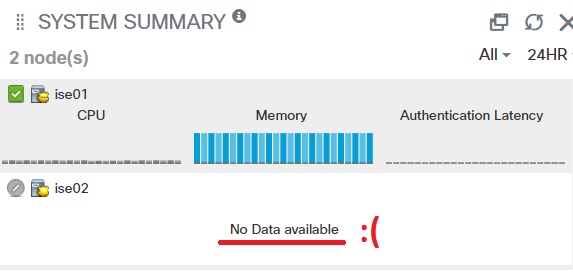
Cisco ISE sometimes fumbles with displaying proper performance graphs for each of the deployments ISE-nodes in the System Summary window, and in this article we take a look at a potential fix that is TAC endorsed.
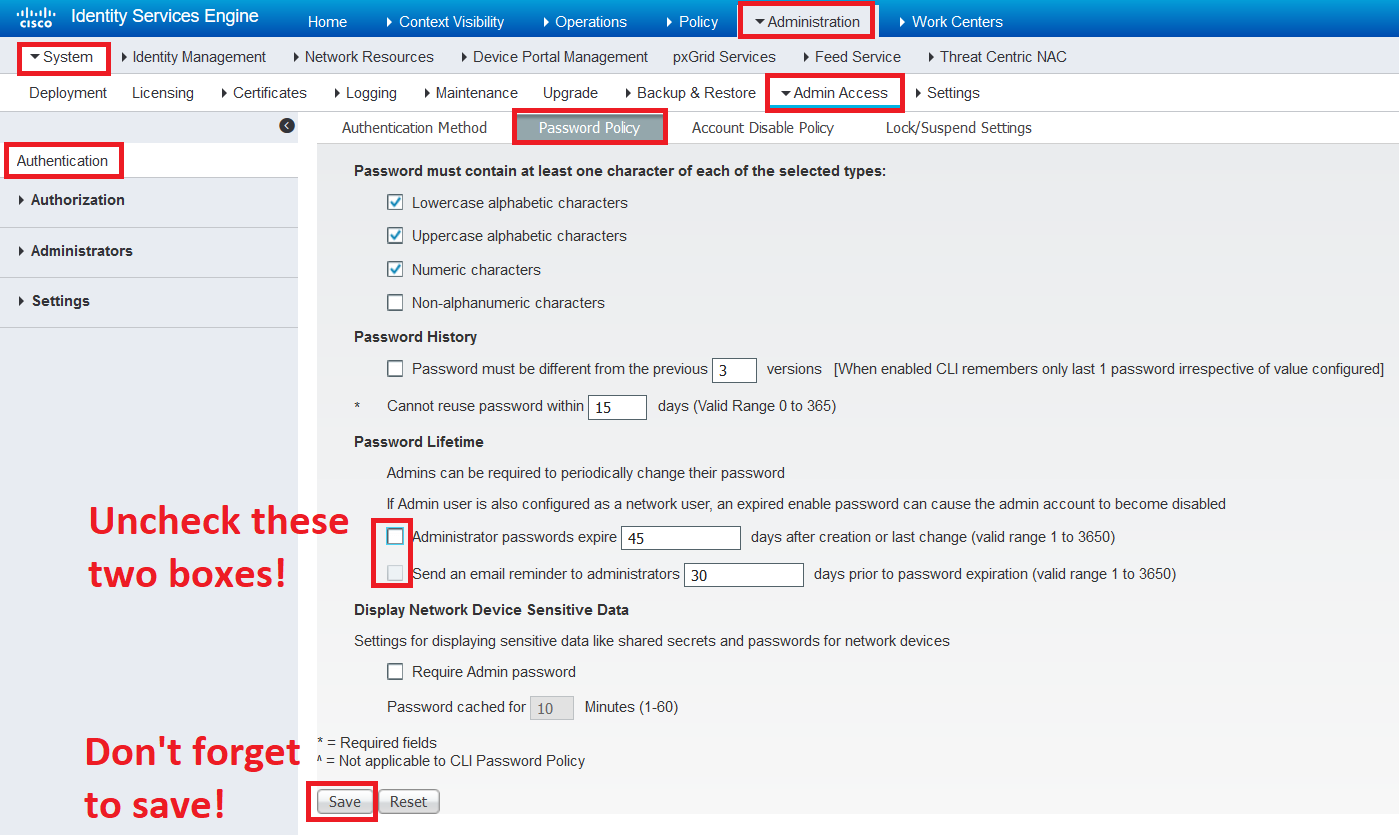
There are a lot of knobs and checkboxes in Cisco’s Identity Services Engine, or ISE, and in this article we go through some general settings that I usually configure when I have a fresh installation of ISE. I’d like to think of them as “good practices” and hopefully, you do too.
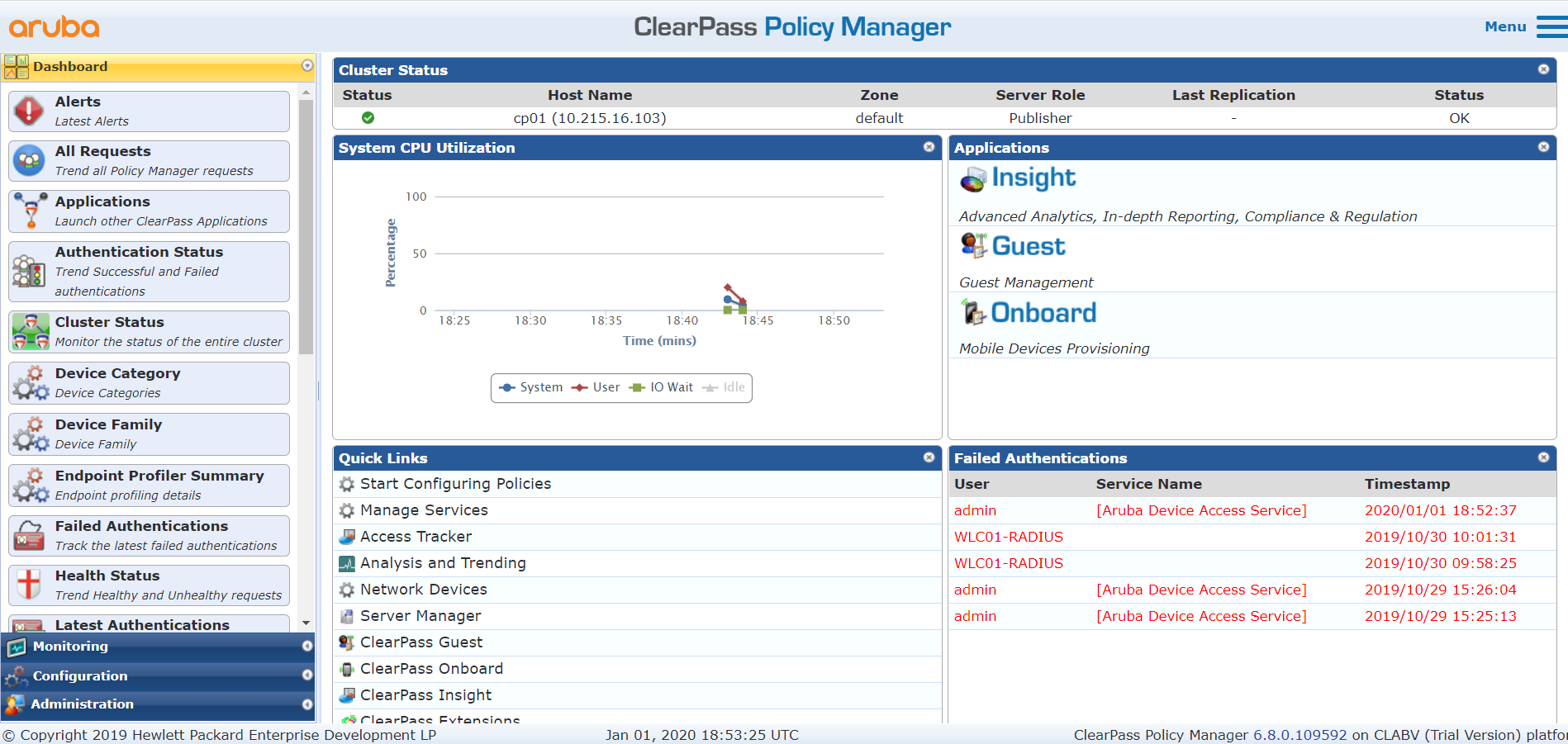
After hearing and reading a lot about HPE/Aruba’s equivalent to Cisco’s ISE, the ClearPass Policy Manager, I got my hands on one to see if I could set it up and get some secure access going. While configuring the system I took some notes on how it differs from Cisco’s ISE solution, let me tell you all about it.
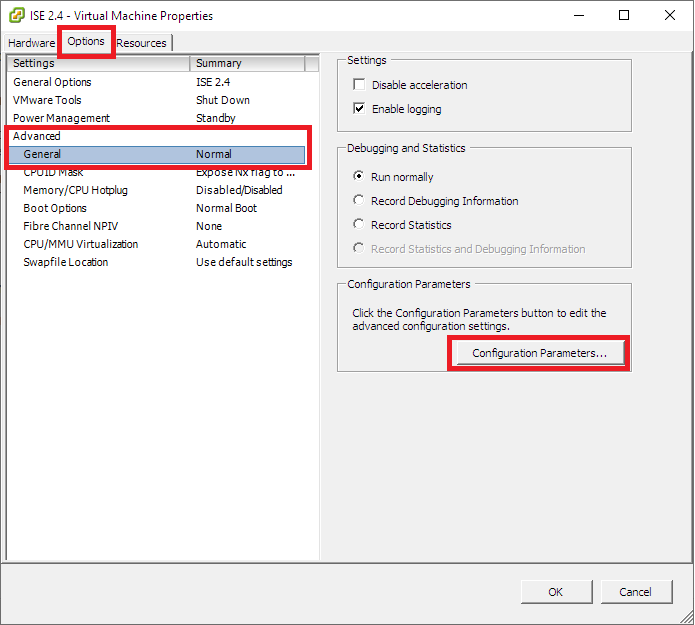
Since a few software versions ago, virtual ISE machines don’t play nice with the snapshot function of a VMware environment, so make use of this easy trick to stay ahead of the game and away from a certain disaster.
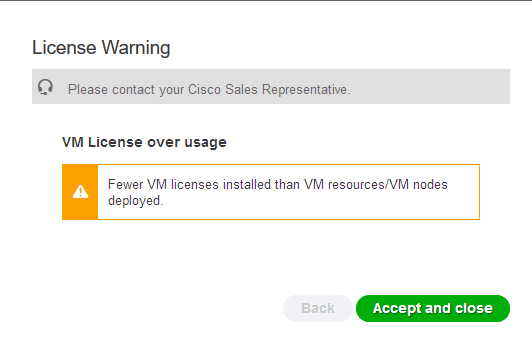
Beginning with ISE version 2.4, Cisco introduced a new type of license for those who have virtual ISE servers instead of physical ones. If your ISE-deployment predates version 2.4 you have the possibility to get your hands on these licenses free-of-charge and you can find out how to do it in this article.
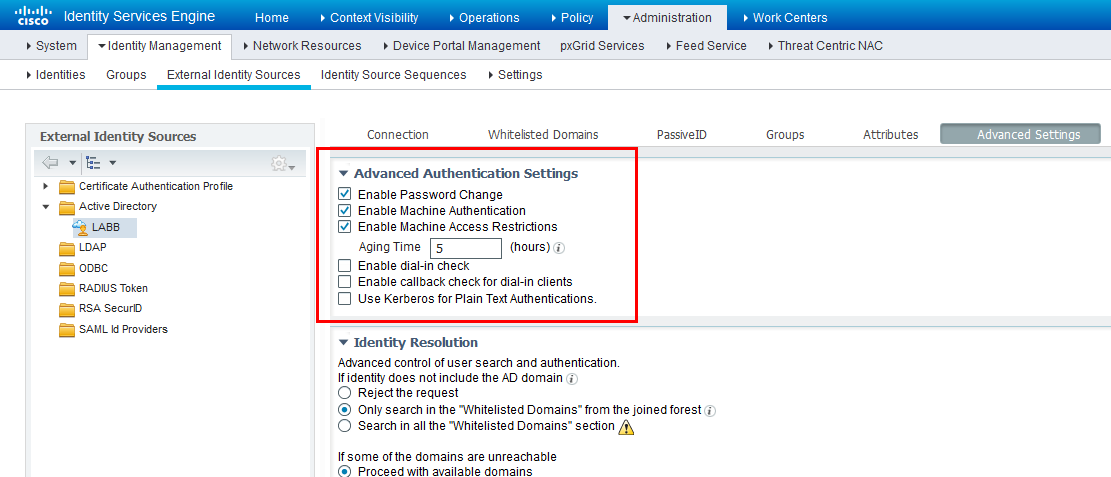
In ISE 2.2 and earlier, keeping track of authenticated computers isn’t as easy as one thinks it should be so in this article we are going to take a look at the ISE feature that is Machine Access Restriction (MAR) Cache and why it’s not always easy to deal with.
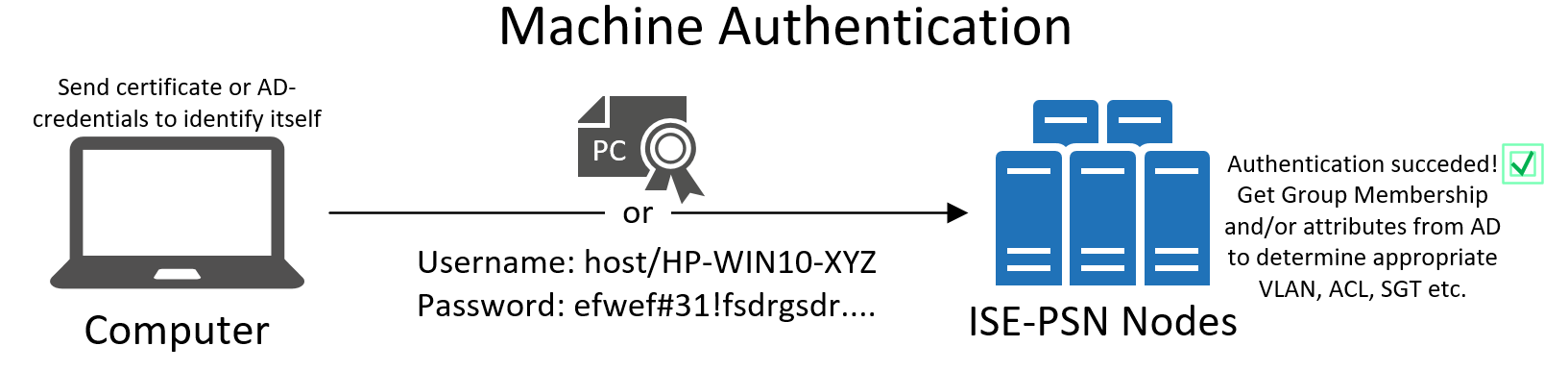
There are a number of way to authenticate users to your network and in this article we take a look the differences between machine (computer) authentication and user authentication in regards to 802.1x (EAP).
Digital Certificate come if a lot of different shapres and are great for managing identification between your services and your users and in this article we take a look at different options regarding the use of certificates in Cisco's Identity Services Engine (ISE).
Windows 10 introduced a lovely security feature called Credential Guard that unfortunately causes a lot of head-aches for us responsible for configuration secure network access in the form of 802.1x (EAP) and in this article your will find out why.
The difference between using PEAP with EAP-TLS as opposed to using “just” EAP-TLS for network access authentication is often misunderstood, and in this article I will attempt to sort out and explain what the difference is.
Android devices for enterprise use are a nightmare to manage ( in my opinion) and in this article we take a look at what the ACL/URL Whitelist for a Cisco WLAN Controller needs to look like in order to support ISE BYOD (Bring-Your-Own-Device) using self-registration for .
Google just had to make some weird changes to Android again in term of network access control so in this article we take a look at the changes in ISE 2.2 regarding the Bring-Your-Own-Device function for Android devices.









In this article, we take a look at the most common pitfalls when it comes to configuring and troubleshooting 802.1x (EAP) authentications in which certificates are involved one way or the other, and what kind of error messages show themselves in different situations.