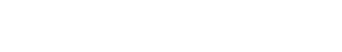
In this article, we take a look to further control how HTTPS Inspection works for your users in different scenarios, by creating a custom Decryption Profile and attaching it to a Decryption Policy Rule.
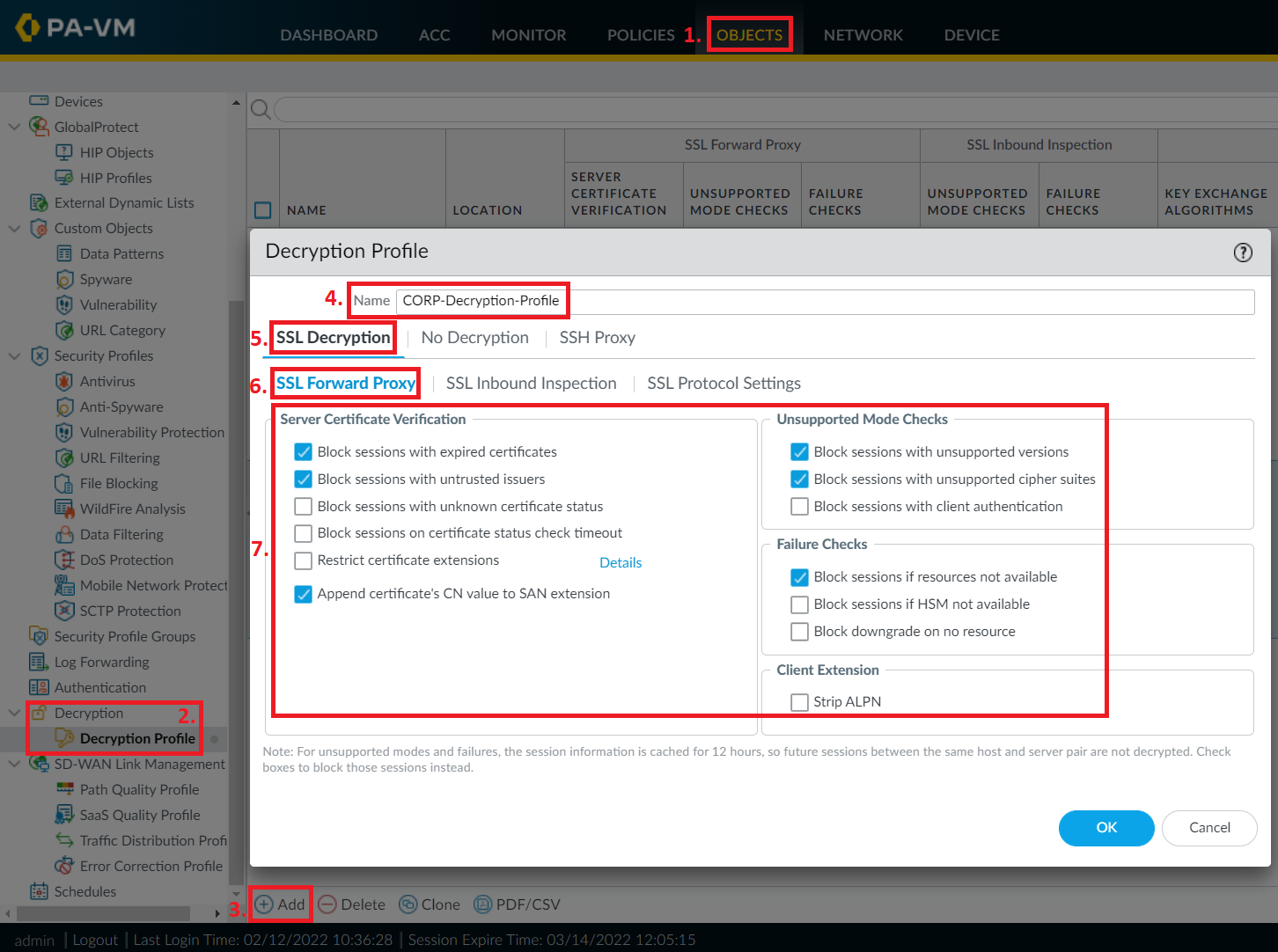
This article deals with HTTPS Inspection using a Root-Signed (by an internal PKI) CA Certificate on a Palo Alto Networks firewall, including adding exceptions to HTTPS Inspection and verifying the feature working properly.
This article deals with HTTPS Inspection using a Self-Signed (by the firewall itself) CA Certificate on a Palo Alto Networks firewall, including adding exceptions to HTTPS Inspection and verifying the feature working properly.
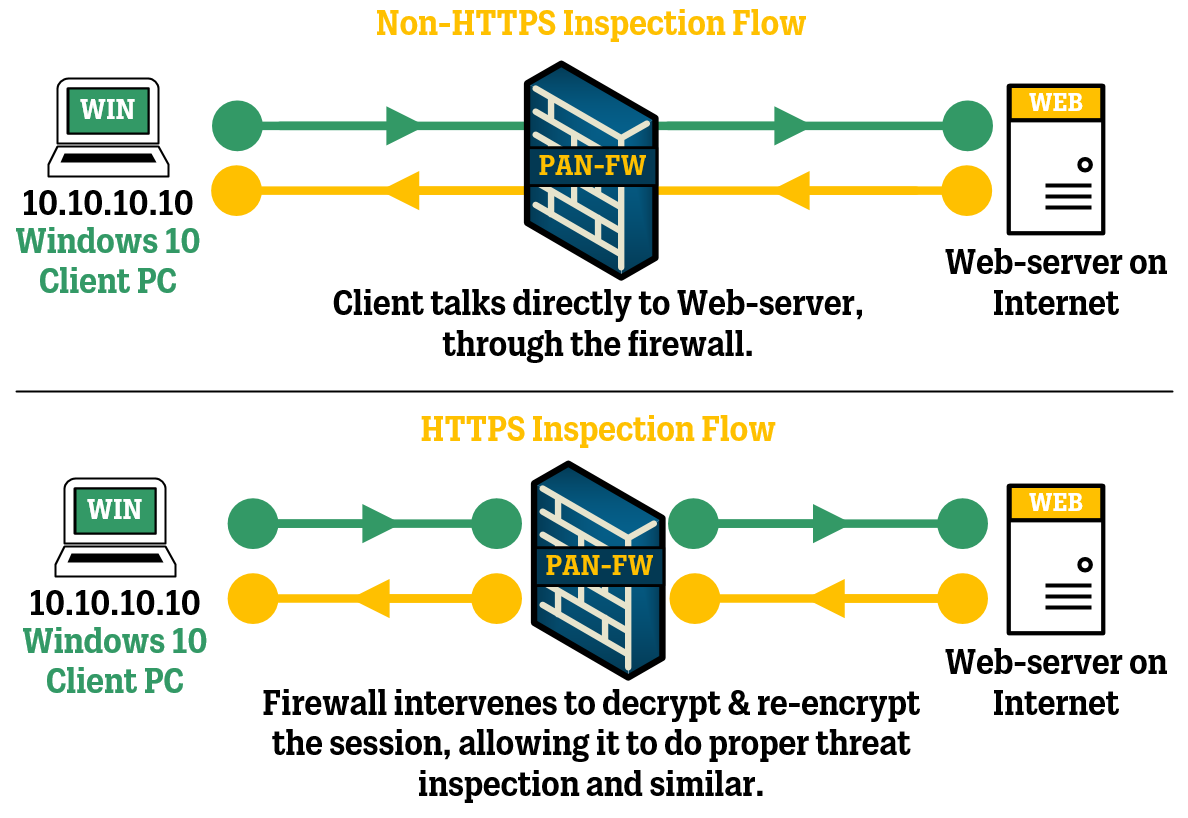
Untrusted websites always suck, whether you run into them online or within your own organization, so in this article we are going to take a look at issuing a proper certificate to our Palo Alto firewall's web interface, and replace the self-signed certificate that is used by default.
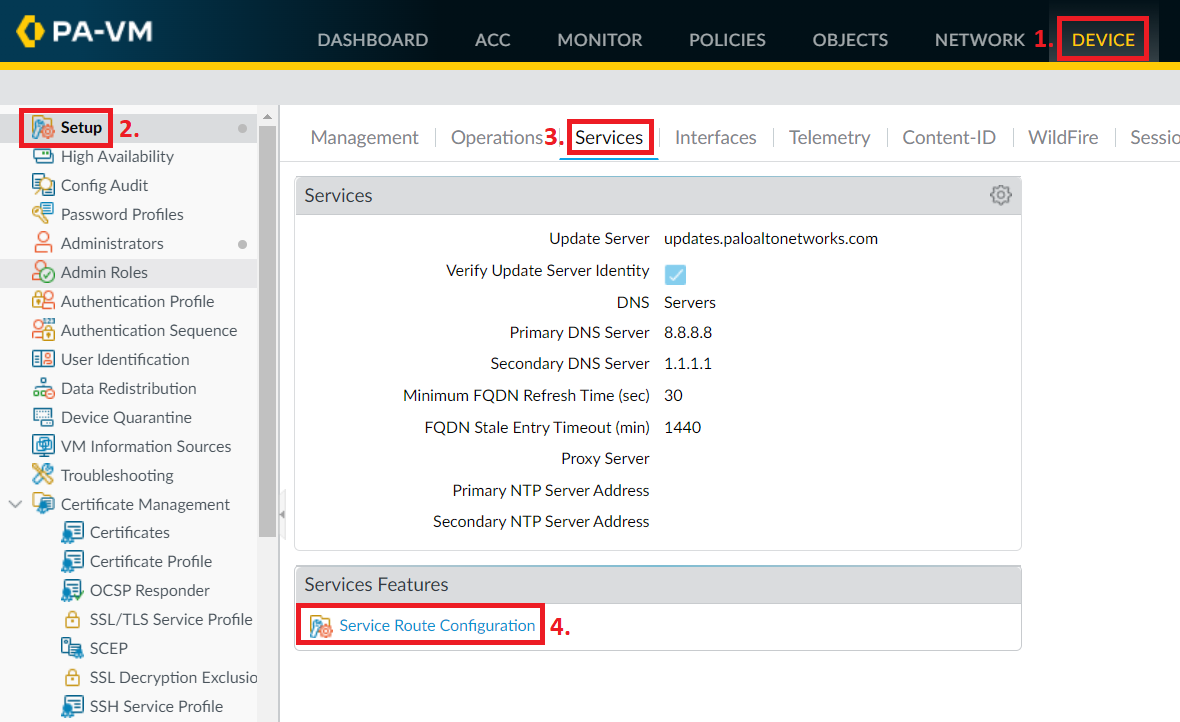
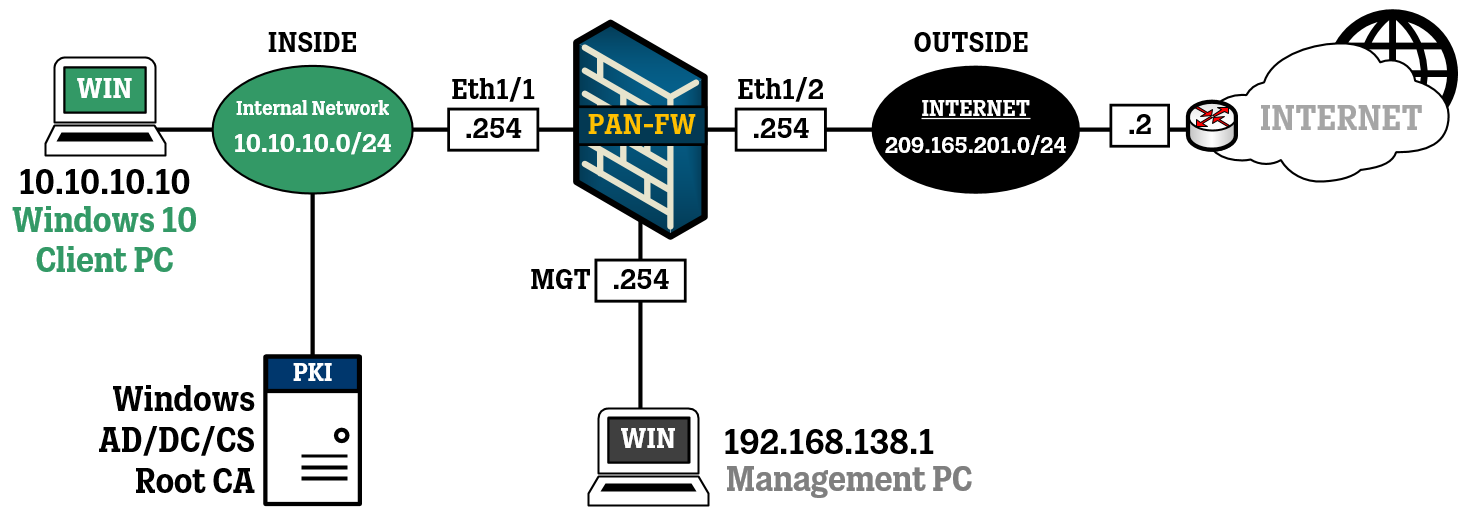
In this article, we take a look at the concept of Service Routes, which are used within Palo Alto firewalls to determine how the firewall communicated with other systems and services for purposes such as authentication, logging and subscription updates to certain features, like URL Filtering.
In this article, we take a look at the initial setup of a virtual, standalone Palo Alto Networks firewall, including some very simple access rules and NAT and useful general settings.

In this article, we take a look at the QUIC protocol and why it might be a good idea to block this protocol entirely if you are using HTTPS Inspection (SSL Outbound Inspection).