This year, I was once again named a Cisco Champion! Click here to read more about what it means and what’s coming next.
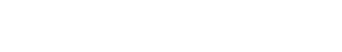
In this article, we take a look at a short snippet of configuration to enable automatic scheduled backup of the running-configuration of Cisco Nexus switches and send the backup file to a remote repository or file server.
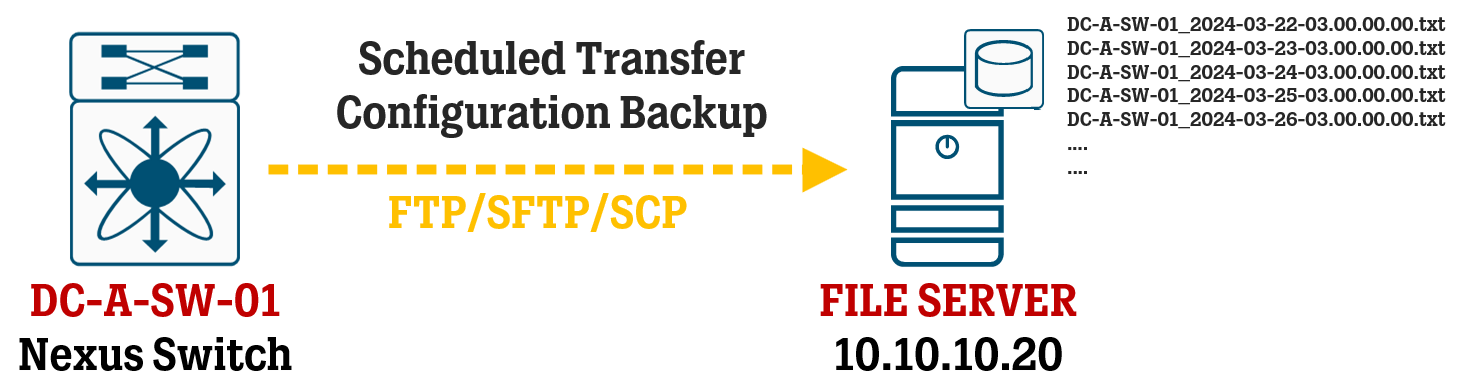
In this article, we take a look at the configuration for implementing NTP with authentication on Cisco IOS-XE devices, both for the NTP Server and NTP Client role, and take a look at common NTP topologies for different use cases.
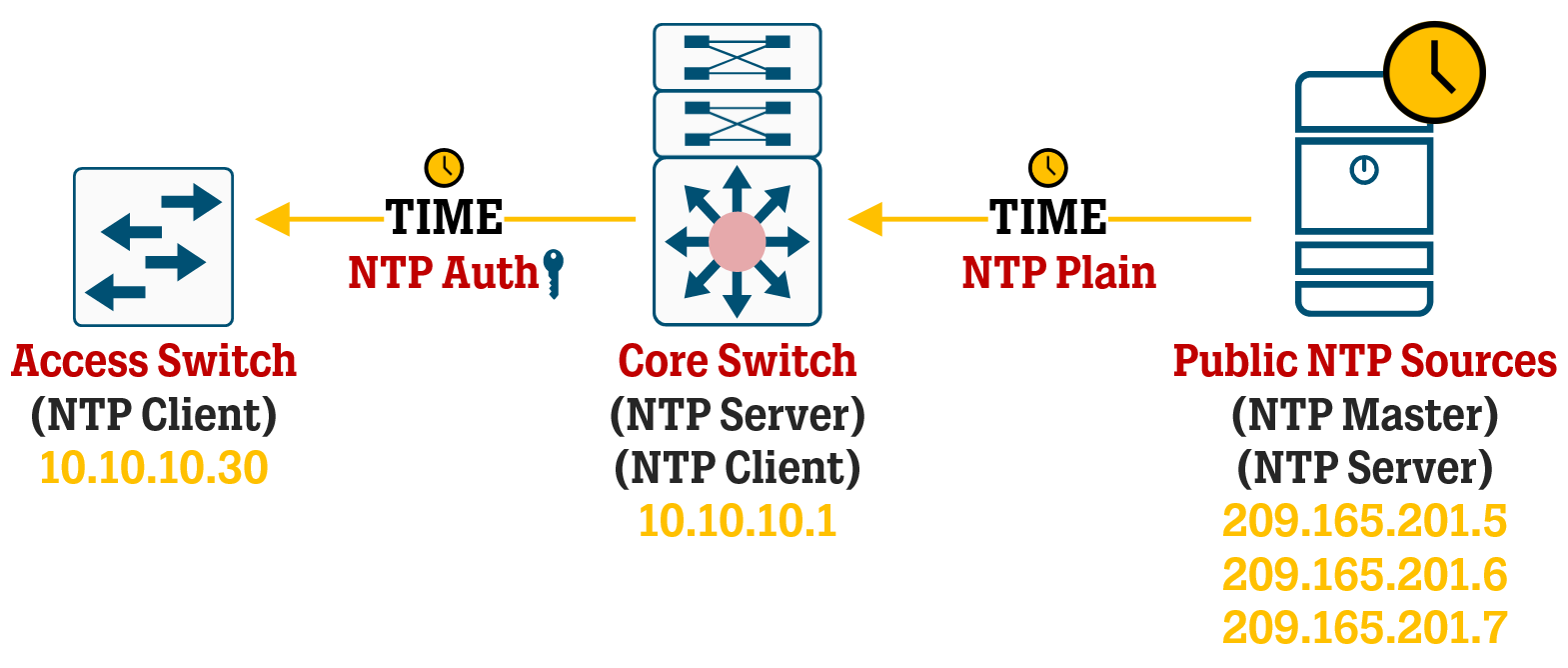
In this article, we take a look at the different use cases of certificates inside Cisco DNA Center, how they are used to establish trust inside your network, and how to set up proper certificate management in your deployment.
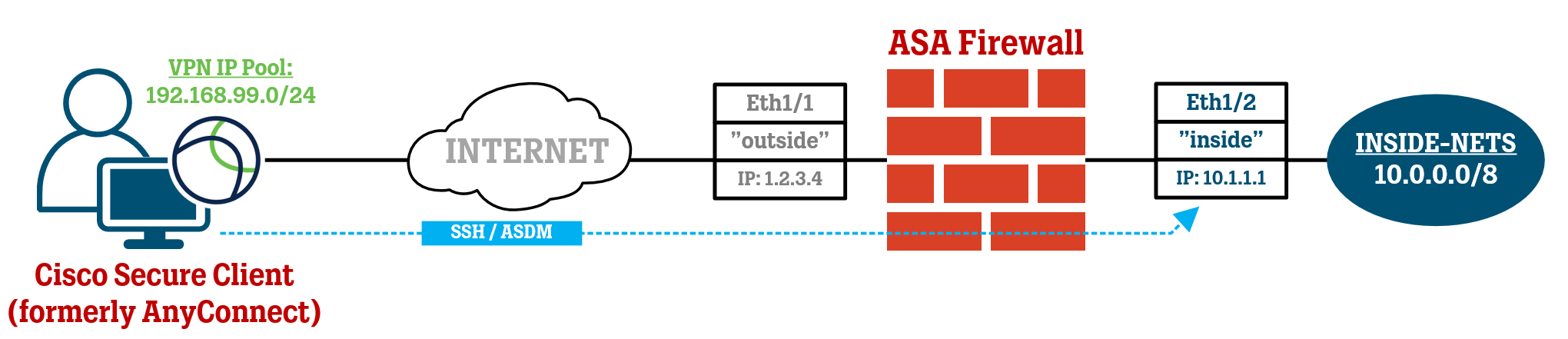
A lot of Cisco ASA administrators run into issues when trying to access the ASA itself over a Remote-Access VPN or Site-to-Site VPN tunnel due to the odd traffic path and in this article, we take a look at some of the fixes you might need to apply to make this all work.
In this article, we take a look at the configuration steps to set up High Availability between two Cisco Secure Firewalls running ASA software using the command line interface (CLI) with a shared dedicated physical link for the Failover and Stateful Link features.
In this article, I’ve compiled a base configuration to be used for setting up new Cisco Adaptive Security Appliances, or ASAs for short, and included some pointers on which other configuration steps are necessary to get most typical deployments up and running.
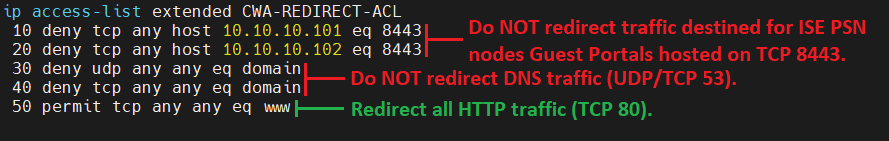
In this short article, we take a look at how to create a Redirection ACL on 9800 WLCs to use with Central Web Authentication for Cisco ISE guest access services and go through what each line of the ACL really does.
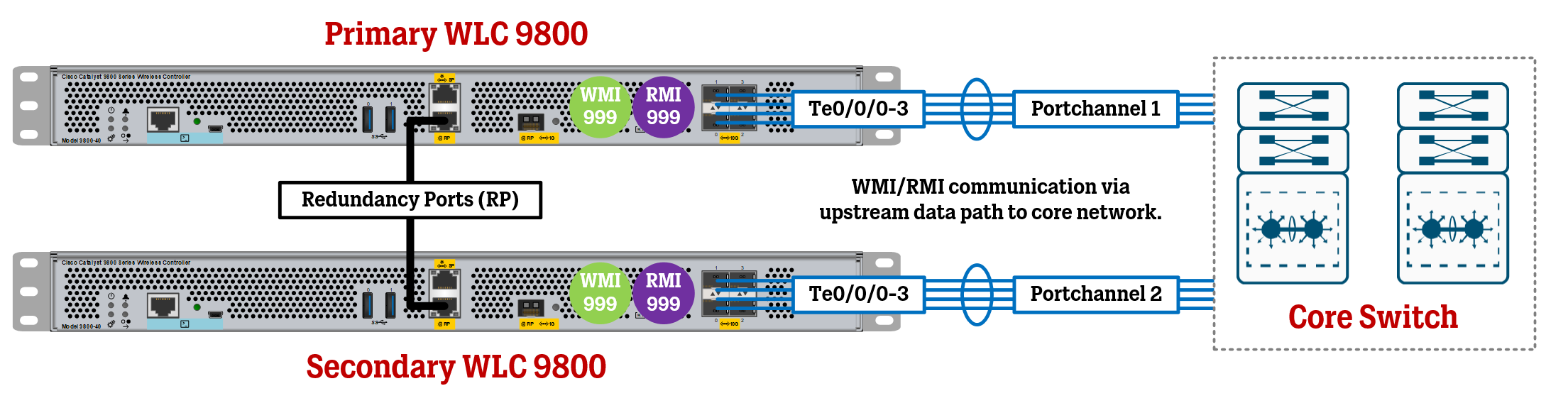
In this article, we take a look at how to configure High Availability Stateful Switchover (HA SSO) on the Cisco 9800 WLCs running IOS-XE using Redundancy Management Interfaces (RMI) in addition to the Redundancy Ports (RP).
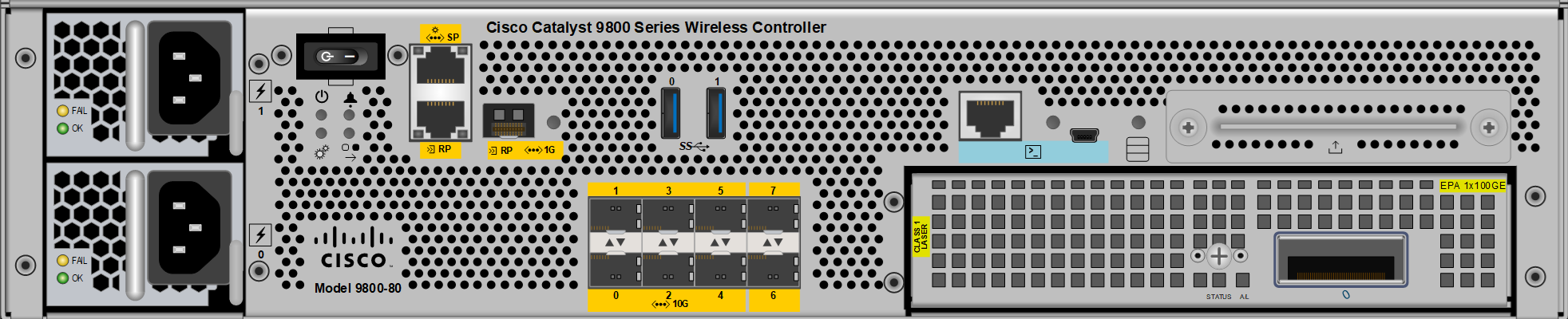
In this article, we take a look at the initial configuration of a Cisco WLC 9800 and some recommended basic general settings that should be a part of most deployments.
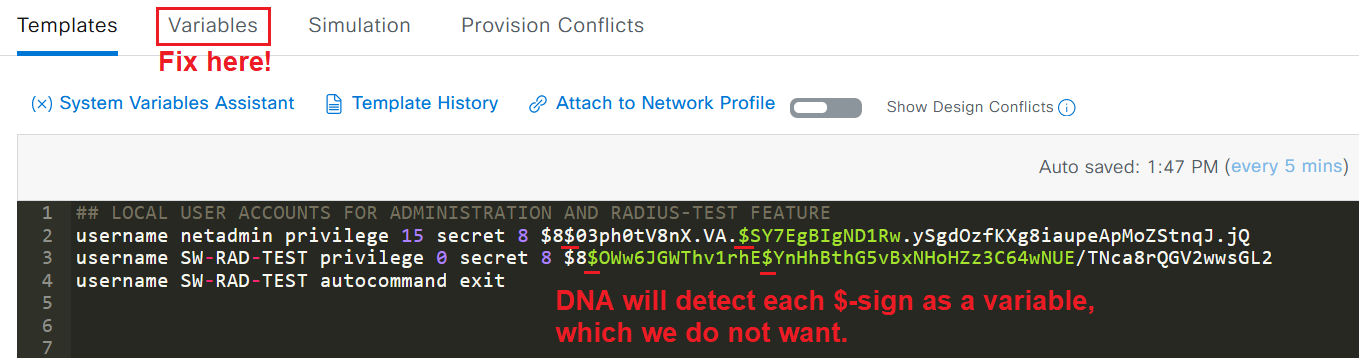
In this article, we take a look at the logic of CLI Template Compliance in Cisco DNA Center and go through some tips on what to consider when you are making CLI Templates of your own that need to be “compliant friendly”.
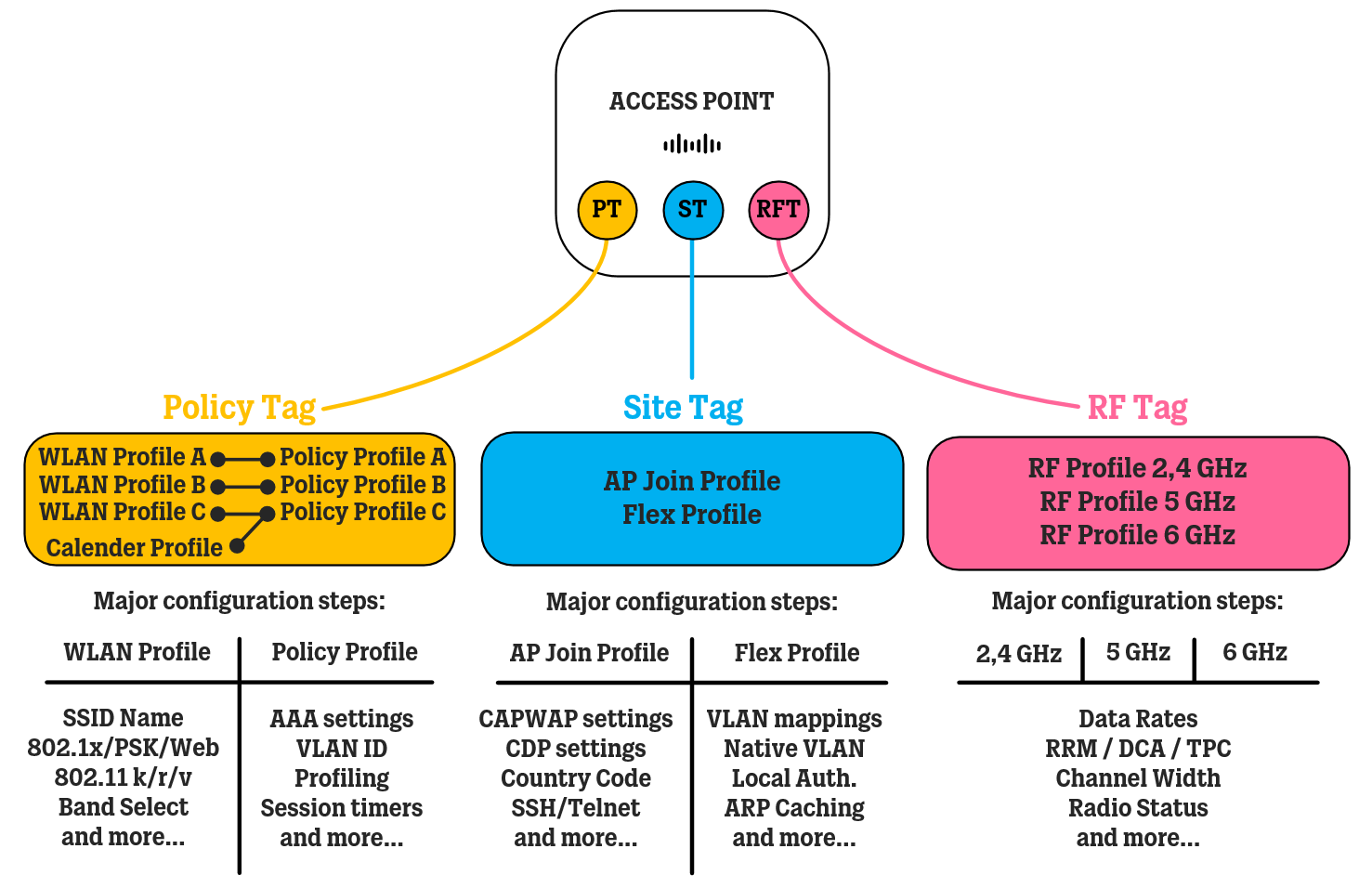
In this article, we take a look at the building blocks of Catalyst 9800 WLAN Controllers configuration, which is very different from the older AireOS WLAN Controllers, and how to organize your configuration in such a way that makes it easier to work with over time.
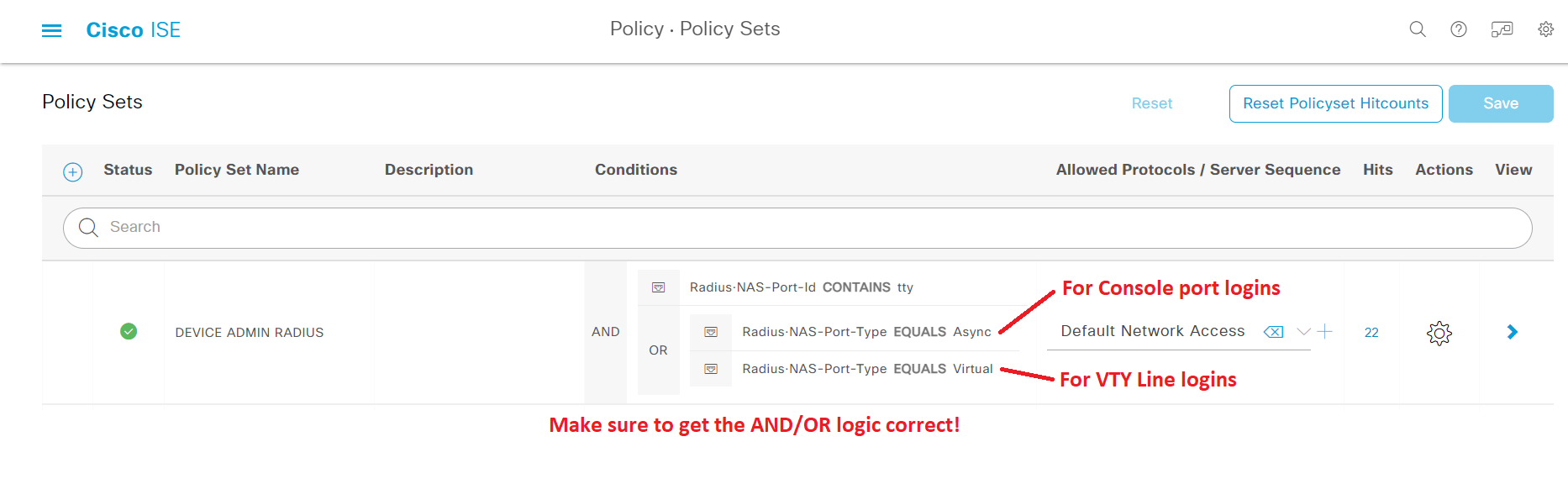
In this article, we look at how to configure Cisco ISE as a RADIUS server to handle authentication requests for controlling access to network devices, both for network administrators with full access and for helpdesk personnel with limited access.
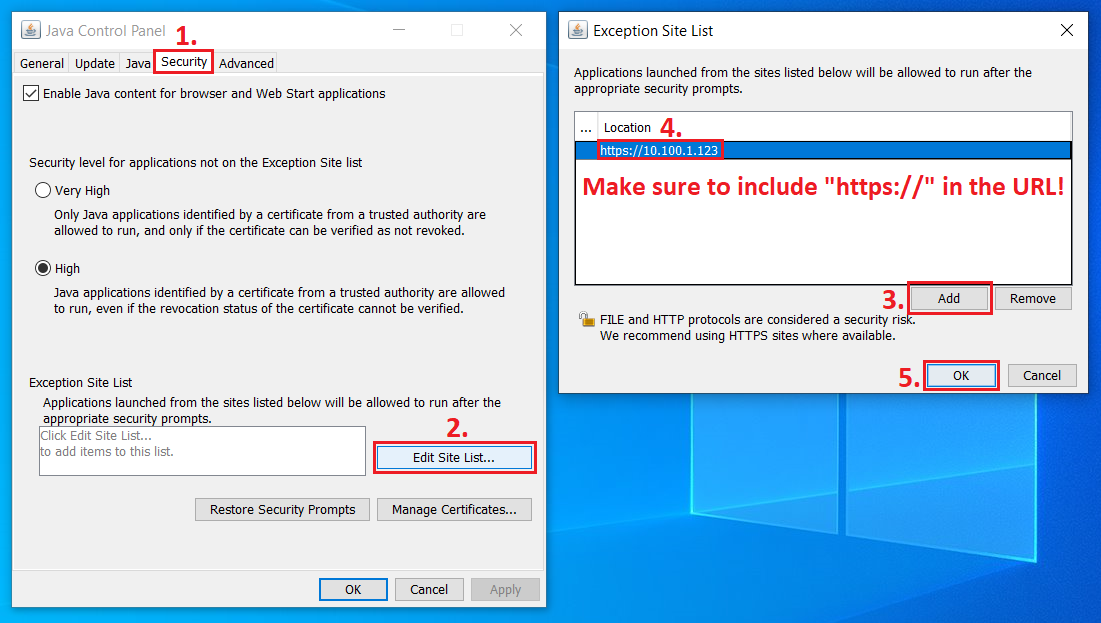
In this article, we take a look at how to configure Java to get Java-based KVM up and running to remotely perform a re-imaging of the Cisco ISE application on physical SNS servers.
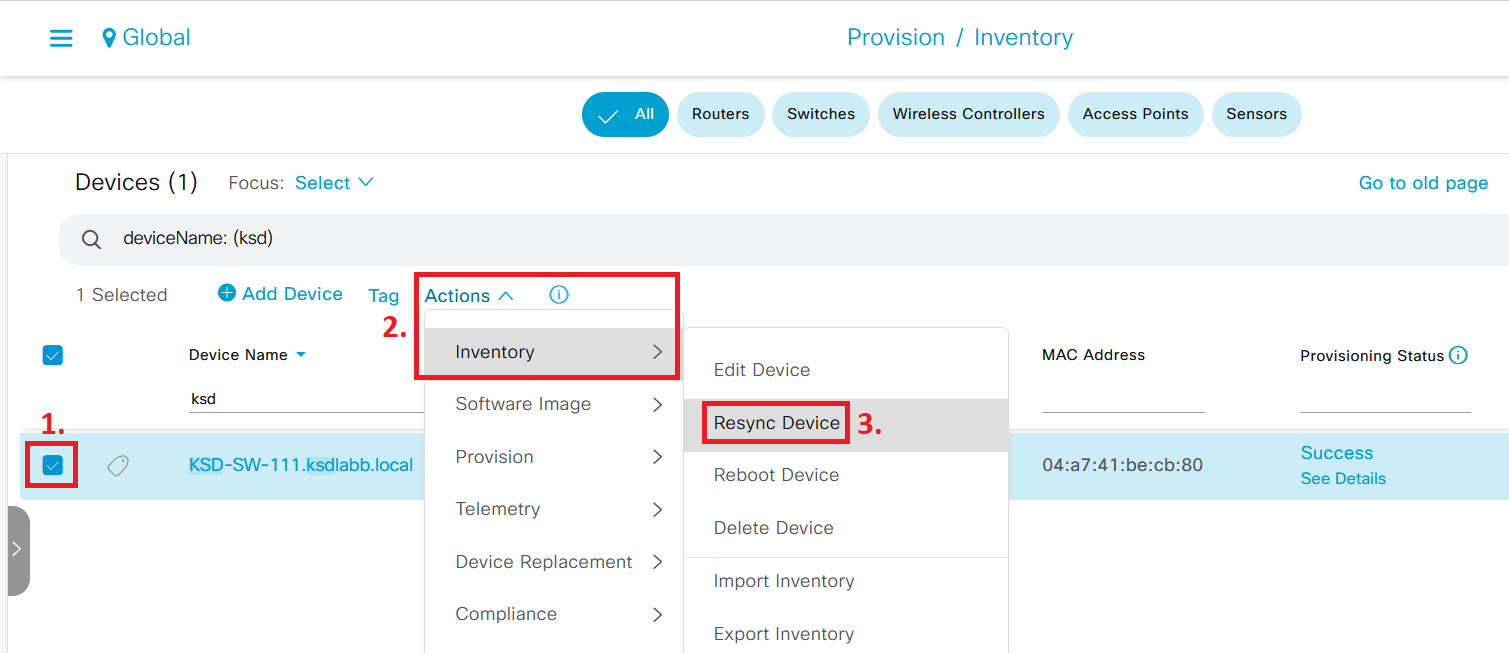
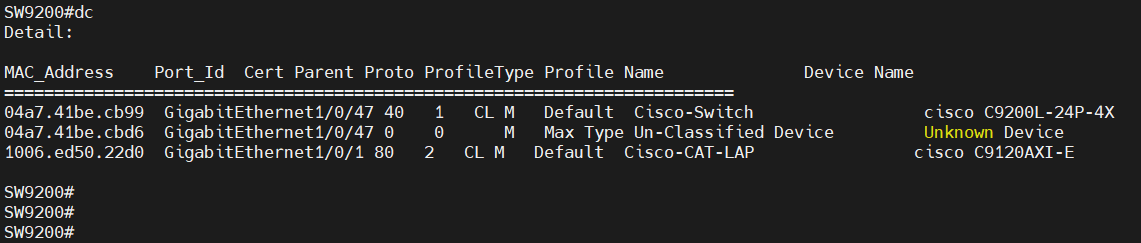
With the rise of powerful network monitoring and automation systems, like Cisco DNA Center, network devices are constantly crawled for status updates. In this article, we look at how this could affect TACACS+ services running on Cisco ISE and what you can do to optimize your deployment.
This year, I was named one of the Cisco Champions of 2023 due to the content I have produced and published on this blog. Click here to read more about what it means and what’s coming next.
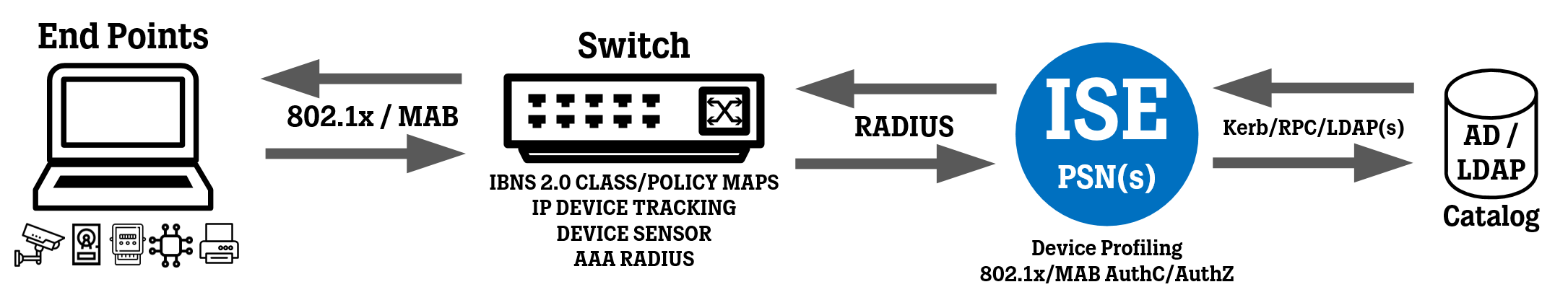
In this article, we take a look at some of the most important “show” commands used when implementing IBNS 2.0 for 802.1x and MAB authentication on Cisco switches, and how to configure Aliases for these commands to dramatically improve time spent on troubleshooting and verification.
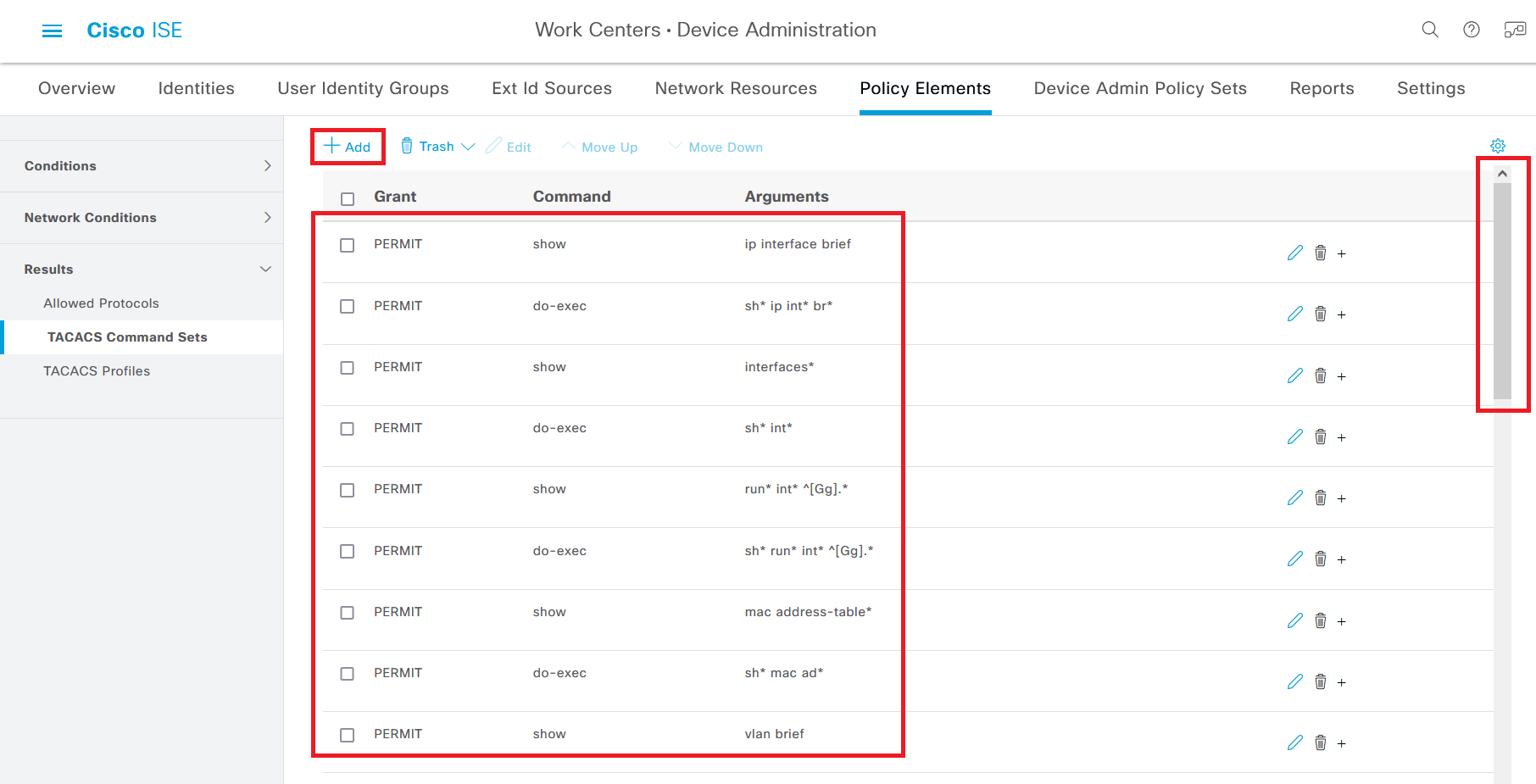
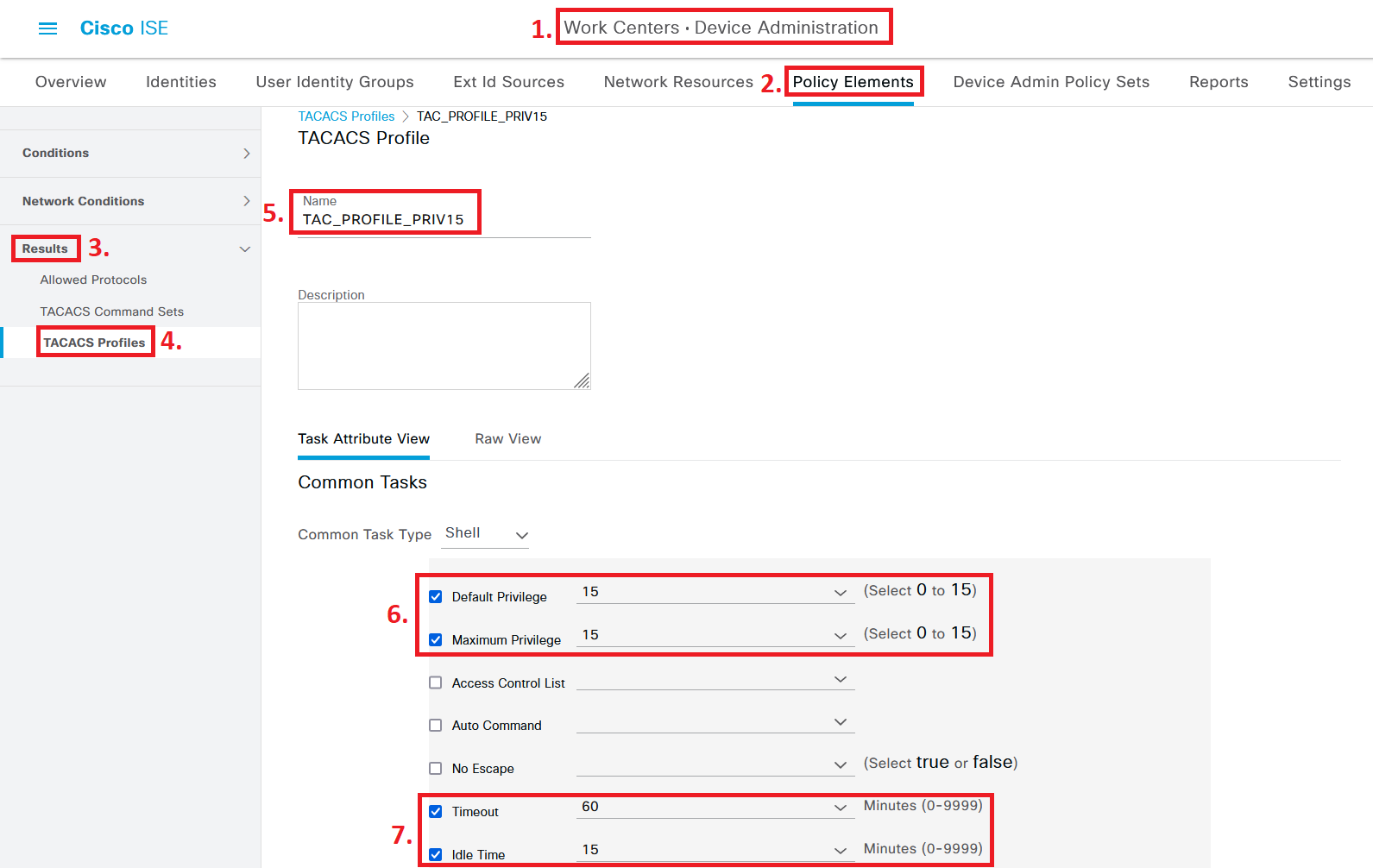
In this article, we take a look at how to configure a TACACS Command Set in Cisco ISE to enable non-administrator staff to use both show commands and configuration commands related to certain interfaces (typically access ports).
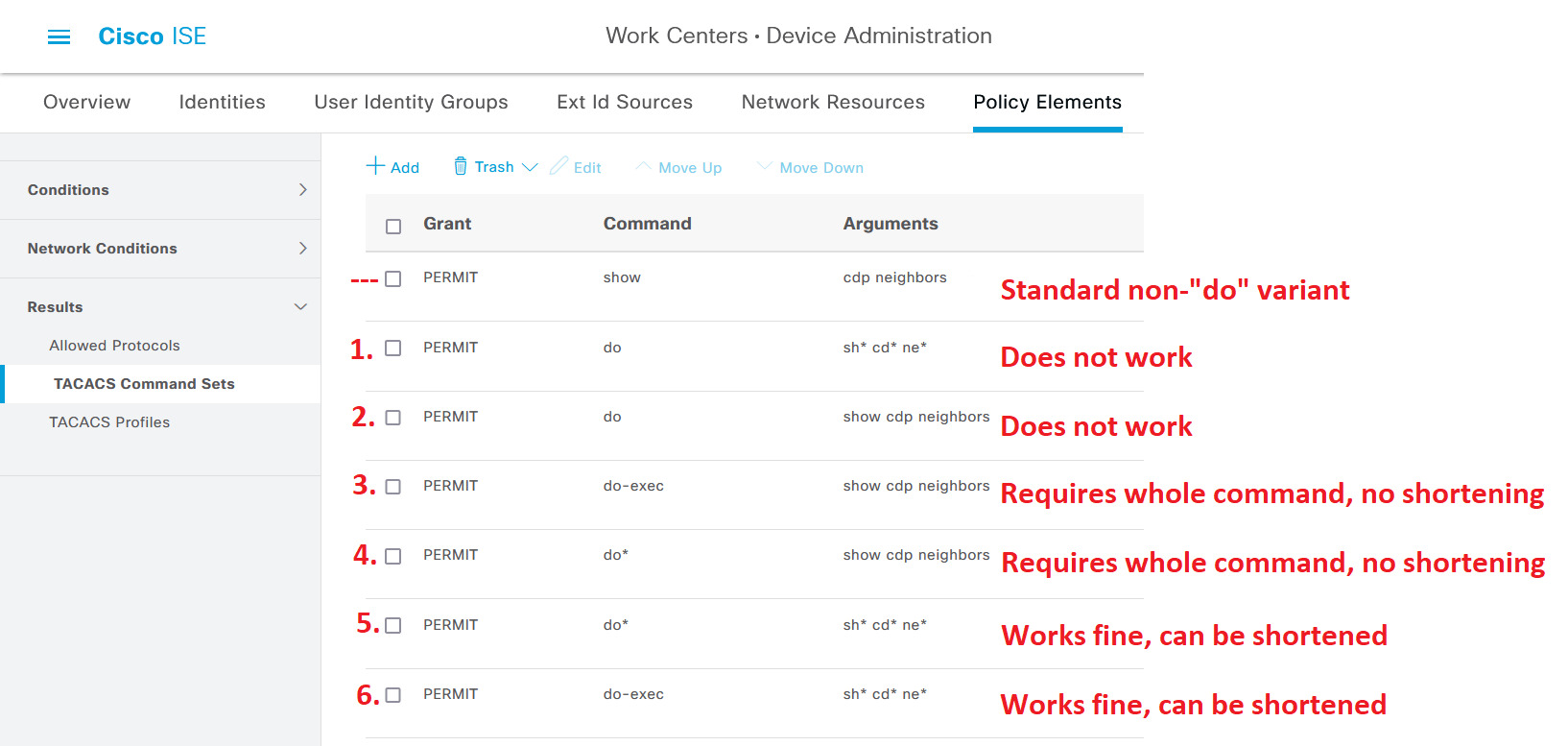
In this article, we are going to take a look at different approaches to enable network administrators to use the “do” command on Cisco network devices where TACACS+ authentication is configured using Cisco ISE.
In this article, we take a look at how to configure Cisco ISE as a TACACS+ server to handle authentication requests for controlling access to network devices, both for network administrators with full access and for helpdesk personnel with limited access.
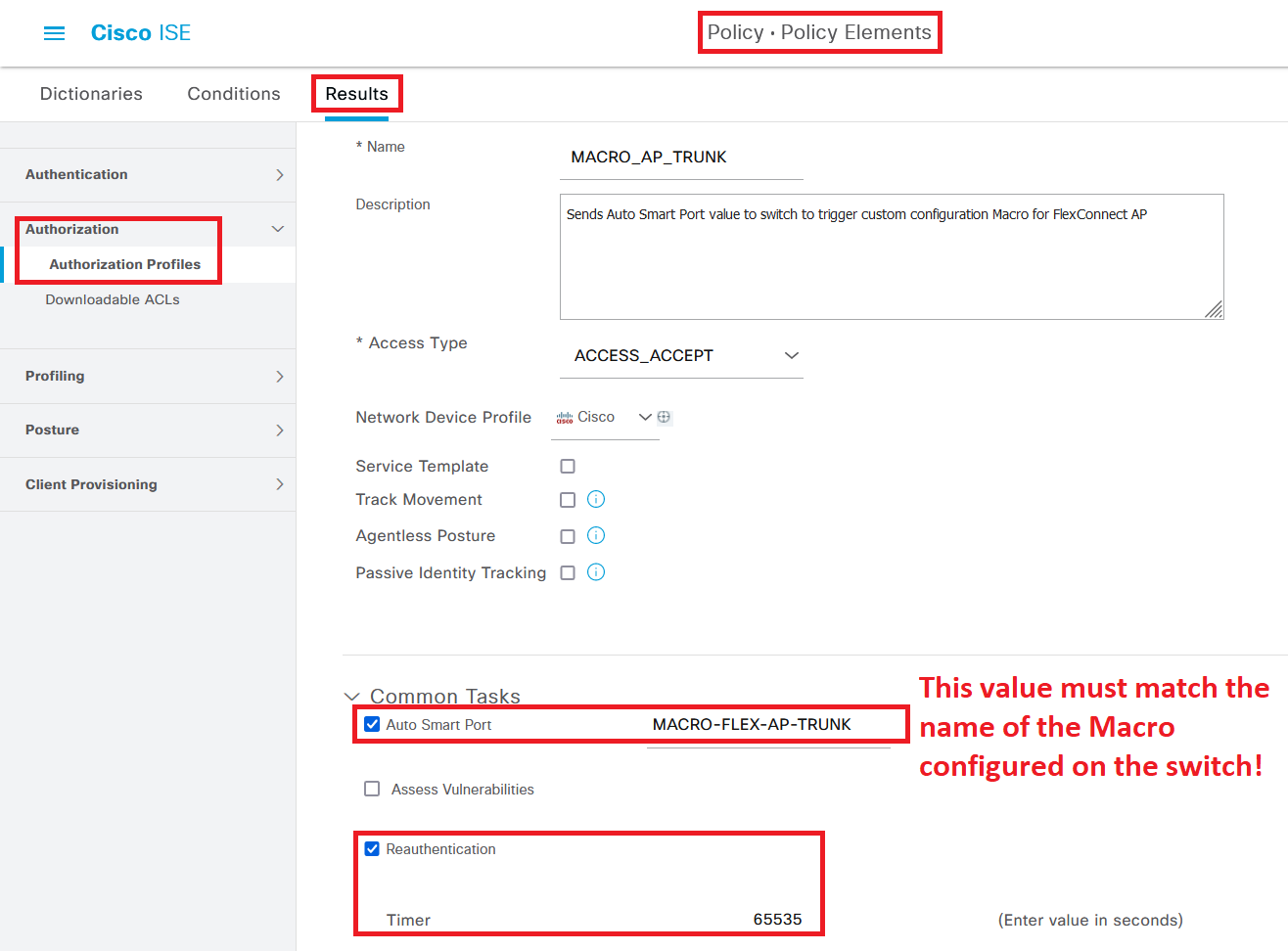
In this article, we take a look at how to make ISE configure a switch port as a Trunk (using a Macro) when an Access Point in FlexConnect mode is connected to an 802.1x/MAB-enabled switch access port, and reverting the configuration back to an access port if the Access Point is unplugged.
In this article, we take a look at a couple of commands that can help your Cisco IBNS 2.0 implementation by going into detail about which kind of events are matched in your Policy Map as endpoints are connected to the network and go through the authentication process.
It’s finally time again! After being an online-only show for the past three years, Cisco Live was finally back as an in-person event. Read what I did at the event, this time taking place in Amsterdam, The Netherlands, as I attended sessions and explored the show floor.
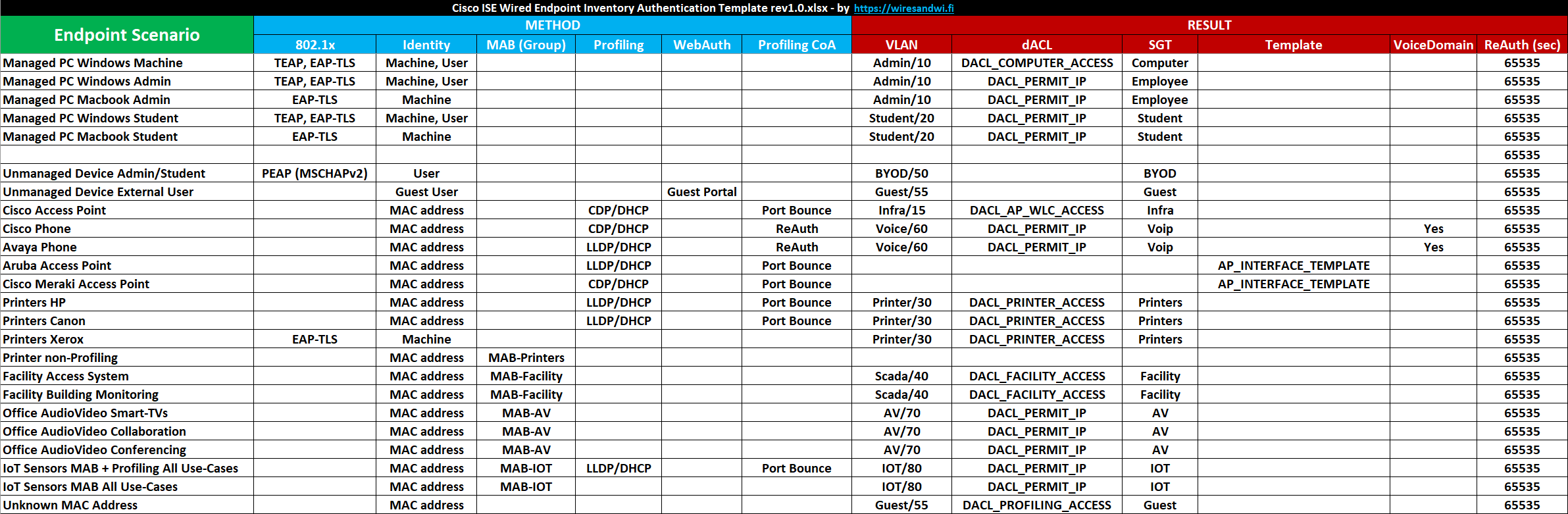
In this article, I share a template you can use for your wired ISE deployments to document which types of endpoints you have in your network, how they will authenticate to the network, and which type of network access they will be granted post-authentication.
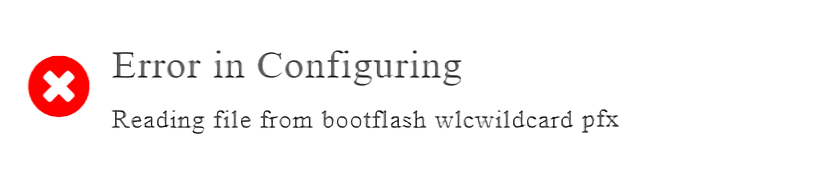
In this article, we take a look at a strange error that can appear when you try to install a certificate in a Cisco WLC 9800, to use for features such as Web Admin or Web Auth guest portals.
In this article, we take a look at a configuration template for deploying IBNS 2.0 Concurrent 802.1x and MAB authentication on Cisco IOS-XE switches, complete with global configuration such as Class Maps, Policy Maps, and Interface configuration.
In this article, we take a look at a configuration template for deploying IBNS 2.0 Concurrent 802.1x and MAB authentication on Cisco IOS switches, complete with global configuration such as Class Maps, Policy Maps, and Interface configuration.
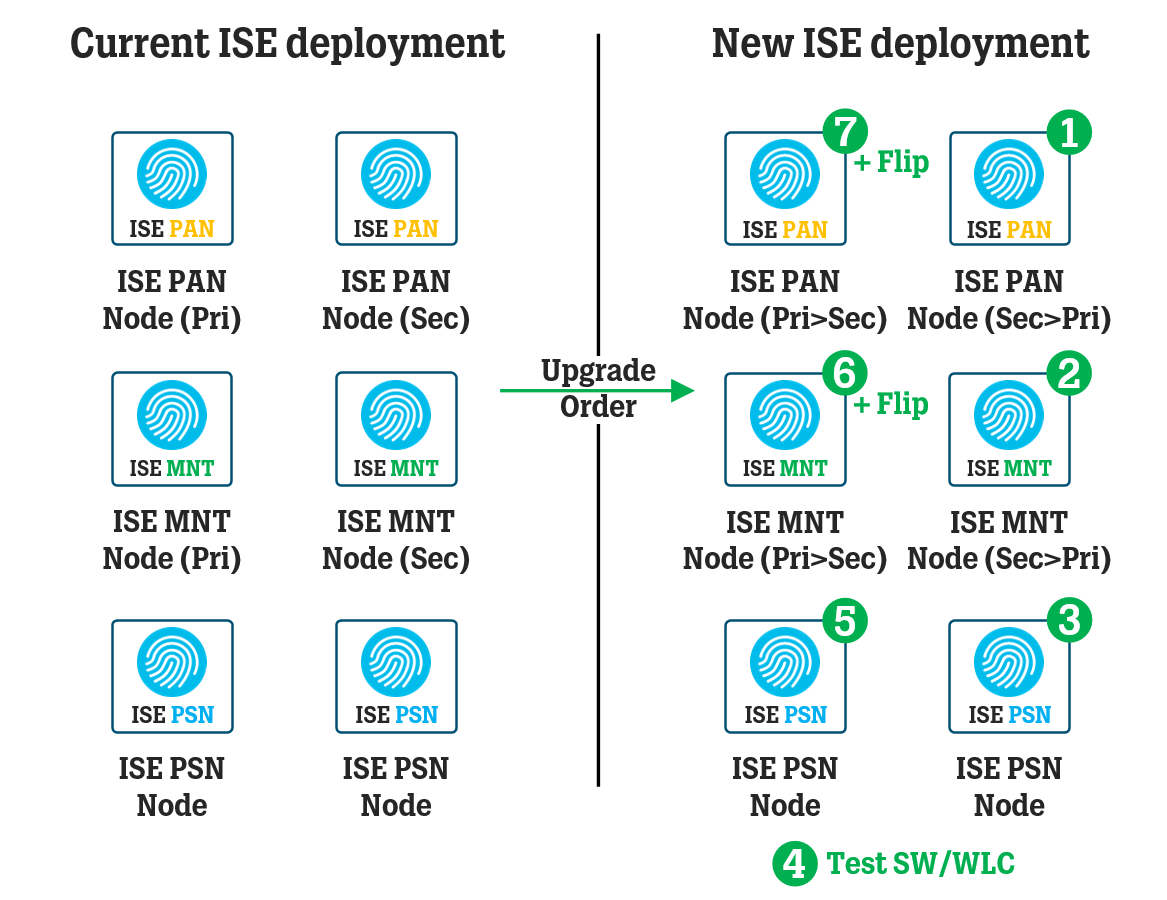
In this article, we take a look at the general steps and processes for upgrading an ISE deployment using the Backup and Restore method, where each ISE node is re-imaged to the new version instead of upgrading existing nodes.
In this article, we take a look at how you can use an Access Control List (“ACL”) to control your ISE PSN nodes available for RADIUS/TACACS communication and how to set up a testing environment halfway through the ISE deployment upgrade process.








In this article, we take a look at the most common pitfalls when it comes to configuring and troubleshooting 802.1x (EAP) authentications in which certificates are involved one way or the other, and what kind of error messages show themselves in different situations.